
SALESFORCE COM INC
FORM 10-Q
(Quarterly Report)
Filed 11/24/10 for the Period Ending 10/31/10
Address THE LANDMARK
ONE MARKET STREET STE.300
SAN FRANCISCO, CA 94105
CIK 0001108524
Symbol CRM
SIC Code 7372 - Prepackaged Software
Industry Software & Programming
Sector Technology
Fiscal Year 01/31
http://www.edgar-online.com
© Copyright 2013, EDGAR Online, Inc. All Rights Reserved.
Distribution and use of this document restricted under EDGAR Online, Inc. Terms of Use.

Table of Contents
UNITED STATES
SECURITIES AND EXCHANGE COMMISSION
Washington, D.C. 20549
FORM 10-Q
(Mark One)
For the quarterly period ended October 31, 2010
OR
Commission File Number: 001-32224
salesforce.com, inc.
(Exact name of registrant as specified in its charter)
The Landmark @ One Market, Suite 300
San Francisco, California 94105
(Address of principal executive offices)
Telephone Number (415) 901-7000
(Registrant’s telephone number, including area code)
Indicate by check mark whether the Registrant (1) has filed all reports required to be filed by Section 13 or 15(d) of the Securities
Exchange Act of 1934 (the “Exchange Act”) during the preceding 12 months (or for such shorter period that the registrant was required to file
such reports), and (2) has been subject to such filing requirements for the past 90 days: Yes No
Indicate by check mark whether the registrant has submitted electronically and posted on its corporate Web site, if any, every Interactive
Data File required to be submitted and posted pursuant to Rule 405 of Regulation S-
T during the preceding 12 months (or for such shorter period
that the registrant was required to submit and post such files). Yes No
Indicate by check mark whether the registrant is a large accelerated filer, an accelerated filer, a non-accelerated filer, or a smaller reporting
company. See the definitions of “large accelerated filer,” “accelerated filer” and “smaller reporting company” in Rule 12b-2 of the Exchange
Act.
Indicate by check mark whether the registrant is a shell company (as defined in Rule 12b-2 of the Exchange Act). Yes No
As of October 31, 2010, there were approximately 131.4 million shares of the Registrant’s Common Stock outstanding.
Quarterly report pursuant to Section 13 or 15(d) of the Securities Exchange Act of 1934
Transition report pursuant to Section 13 or 15(d) of the Securities Exchange Act of 1934
Delaware
94
-
3320693
(State or other jurisdiction of
incorporation or organization)
(IRS Employer
Identification No.)
Large accelerated filer
Accelerated filer
Non
-
accelerated filer
(Do not check if a smaller reporting company)
Smaller reporting company

Table of Contents
salesforce.com, inc.
INDEX
2
Page No.
PART I. FINANCIAL INFORMATION
Item 1.
Condensed Consolidated Financial Statements:
Condensed Consolidated Balance Sheets as of October 31, 2010 and January 31, 2010
3
Condensed Consolidated Statements of Operations for the three and nine months ended October 31, 2010 and
2009
4
Condensed Consolidated Statements of Cash Flows for the three and nine months ended October 31, 2010 and
2009
5
Notes to Condensed Consolidated Financial Statements
6
Item 2.
Management
’
s Discussion and Analysis of Financial Condition and Results of Operations
30
Item 3.
Quantitative and Qualitative Disclosures About Market Risk
49
Item 4.
Controls and Procedures
50
PART II. OTHER INFORMATION
Item 1.
Legal Proceedings and Claims
51
Item 1A.
Risk Factors
51
Item 2.
Unregistered Sales of Equity Securities and Use of Proceeds
68
Item 3.
Defaults Upon Senior Securities
68
Item 4.
Removed and Reserved
68
Item 5.
Other Information
68
Item 6.
Exhibits
68
Signatures
69

Table of Contents
PART I. FINANCIAL INFORMATION
salesforce.com, inc.
Condensed Consolidated Balance Sheets
(in thousands)
See accompanying Notes to Condensed Consolidated Financial Statements.
3
ITEM 1.
CONDENSED CONSOLIDATED FINANCIAL STATEMENTS
October 31,
2010
January 31,
2010
(unaudited)
Assets
Current assets:
Cash and cash equivalents
$
630,303
$
1,011,306
Short
-
term marketable securities
139,545
230,659
Accounts receivable, net
258,764
320,956
Deferred commissions
50,361
47,388
Deferred income taxes
49,620
40,116
Prepaid expenses and other current assets
64,343
55,734
Total current assets
1,192,936
1,706,159
Marketable securities, noncurrent
1,032,592
485,083
Fixed assets, net
116,078
89,711
Deferred commissions, noncurrent
32,856
28,140
Deferred income taxes, noncurrent
30,501
27,579
Capitalized software, net
79,499
34,809
Goodwill
187,038
48,955
Other assets, net
69,194
39,765
Total assets
$
2,740,694
$
2,460,201
Liabilities and stockholders
’
equity
Current liabilities:
Accounts payable
$
23,320
$
14,791
Accrued expenses and other current liabilities
287,627
194,738
Income taxes payable
9,644
8,424
Deferred revenue
672,454
690,177
Total current liabilities
993,045
908,130
0.75% Convertible senior notes due 2015, net
466,847
450,198
Income taxes payable, noncurrent
18,284
17,551
Long
-
term lease liabilities and other
27,949
13,485
Deferred revenue, noncurrent
22,103
14,171
Total liabilities
1,528,228
1,403,535
salesforce.com stockholders
’
equity:
Common stock
131
127
Additional paid
-
in capital
1,041,005
938,544
Accumulated other comprehensive gain (loss)
9,030
(1,430
)
Retained earnings
160,122
106,561
Total stockholders
’
equity controlling interest
1,210,288
1,043,802
Total stockholders
’
equity noncontrolling interest
2,178
12,864
Total stockholders
’
equity
1,212,466
1,056,666
Total liabilities and stockholders
’
equity
$
2,740,694
$
2,460,201
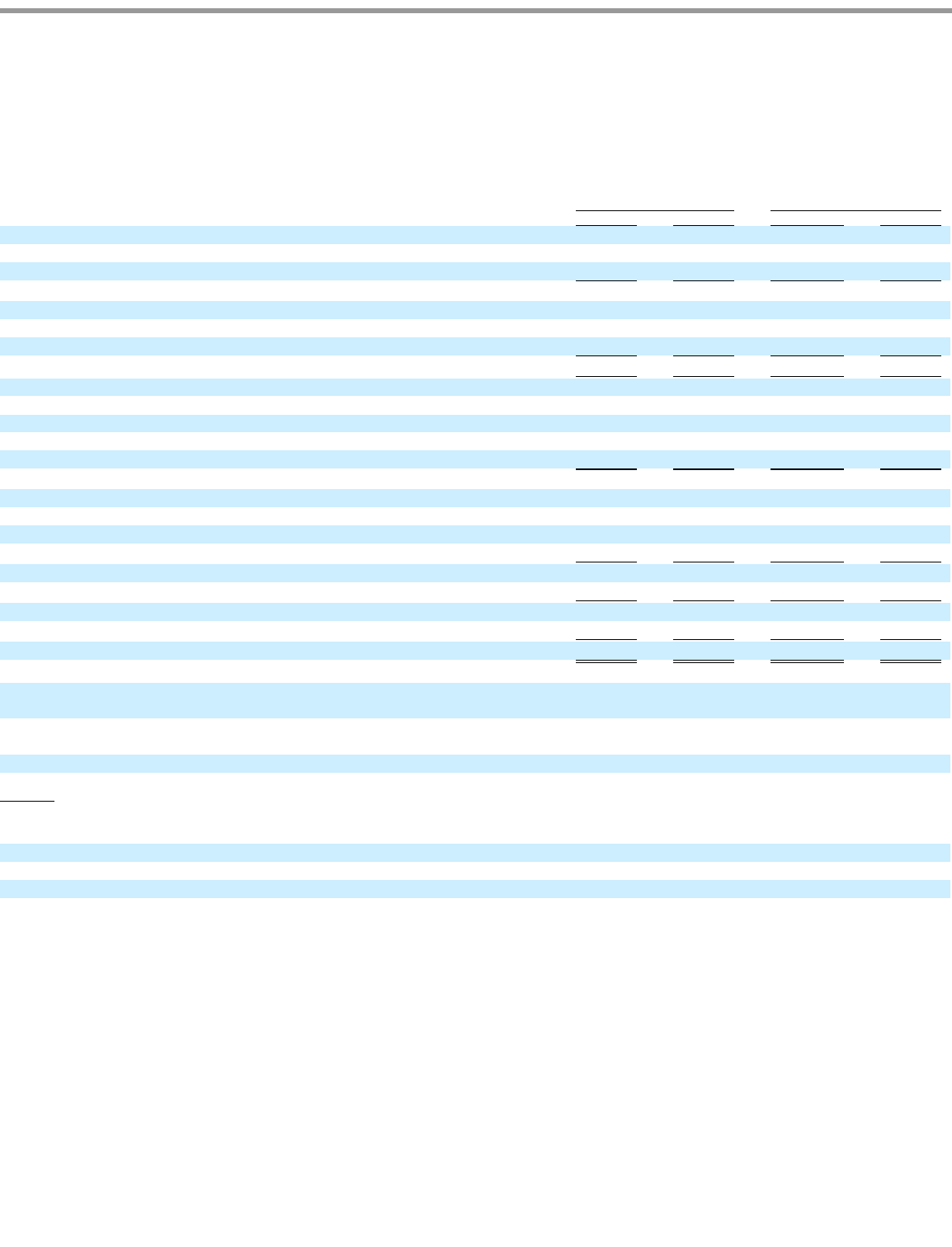
Table of Contents
salesforce.com, inc.
Condensed Consolidated Statements of Operations
(in thousands, except per share data)
(unaudited)
See accompanying Notes to Condensed Consolidated Financial Statements.
4
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Revenues:
Subscription and support
$
402,948
$
306,870
$
1,122,611
$
882,078
Professional services and other
26,139
23,679
77,661
69,456
Total revenues
429,087
330,549
1,200,272
951,534
Cost of revenues (1):
Subscription and support
54,089
40,745
147,127
116,744
Professional services and other
28,042
24,825
84,375
73,122
Total cost of revenues
82,131
65,570
231,502
189,866
Gross profit
346,956
264,979
968,770
761,668
Operating expenses (1):
Research and development
47,305
32,763
130,357
95,450
Marketing and sales
200,544
152,166
558,812
436,647
General and administrative
63,951
49,909
181,713
139,818
Total operating expenses
311,800
234,838
870,882
671,915
Income from operations
35,156
30,141
97,888
89,753
Investment income
11,699
7,503
28,309
19,780
Interest expense
(7,374
)
(292
)
(21,619
)
(793
)
Other expense
(921
)
(336
)
(4,659
)
(1,037
)
Income before provision for income taxes and noncontrolling interest
38,560
37,016
99,919
107,703
Provision for income taxes
(16,192
)
(15,573
)
(41,092
)
(45,426
)
Consolidated net income
22,368
21,443
58,827
62,277
Less: Net income attributable to noncontrolling interest
(1,296
)
(752
)
(5,266
)
(1,952
)
Net income attributable to salesforce.com
$
21,072
$
20,691
$
53,561
$
60,325
Earnings per share
—
basic and diluted:
Basic net income per share attributable to salesforce.com common
shareholders
$
0.16
$
0.17
$
0.41
$
0.49
Diluted net income per share attributable to salesforce.com common
shareholders
$
0.15
$
0.16
$
0.40
$
0.48
Shares used in computing basic net income per share
130,888
124,561
129,461
123,871
Shares used in computing diluted net income per share
137,044
128,596
135,007
126,993
(1) Amounts include stock
-
based expenses, as follows:
Cost of revenues
$
2,357
$
2,995
$
8,617
$
9,322
Research and development
3,976
2,707
12,119
8,741
Marketing and sales
11,969
9,055
36,496
28,314
General and administrative
7,330
5,650
21,483
16,570

Table of Contents
salesforce.com, inc.
Condensed Consolidated Statements of Cash Flows
(in thousands)
(unaudited)
See accompanying Notes to Condensed Consolidated Financial Statements.
5
Three Months Ended
October 31,
Nine Months Ended
October 31,
2010
2009
2010
2009
Operating activities:
Consolidated net income
$
22,368
$
21,443
$
58,827
$
62,277
Adjustments to reconcile net income to net cash provided by operating
activities:
Depreciation and amortization
19,710
13,601
52,008
37,890
Amortization of debt discount and transaction costs
6,655
—
17,639
—
Amortization of deferred commissions
19,959
15,698
57,554
45,959
Expenses related to stock
-
based awards
25,632
20,407
78,715
62,947
Excess tax benefits from employee stock plans
(14,578
)
(7,401
)
(46,768
)
(32,536
)
Changes in assets and liabilities:
Accounts receivable, net
(30,212
)
(22,515
)
67,326
75,355
Deferred commissions
(25,687
)
(18,013
)
(65,243
)
(43,018
)
Prepaid expenses and other current assets
(16,583
)
(12,892
)
(6,463
)
(14,711
)
Other assets
(5,263
)
(506
)
(9,405
)
(624
)
Accounts payable
2,575
2,228
6,500
(762
)
Accrued expenses and other current liabilities
57,926
27,045
95,320
35,165
Deferred revenue
11,538
(3,575
)
(12,691
)
(48,591
)
Net cash provided by operating activities
74,040
35,520
293,319
179,351
Investing activities:
Business combinations, net of cash acquired
(3,834
)
(4,500
)
(155,337
)
(4,500
)
Land activity
(8,000
)
—
(
8,000
)
—
Investments in privately
-
held companies
(4,000
)
(3,700
)
(6,500
)
(4,400
)
Purchases of marketable securities
(296,557
)
(218,056
)
(1,518,996
)
(980,519
)
Sales of marketable securities
518,641
121,413
868,595
438,679
Maturities of marketable securities
58,256
55,400
200,768
119,566
Capital expenditures
(20,790
)
(10,389
)
(60,311
)
(42,445
)
Net cash provided by (used in) investing activities
243,716
(59,832
)
(679,781
)
(473,619
)
Financing activities:
Purchase of subsidiary stock
(150,970
)
—
(
152,243
)
—
Proceeds from the exercise of stock options
44,353
18,559
115,996
32,866
Excess tax benefits from employee stock plans
14,578
7,401
46,768
32,536
Principal payments on capital lease obligations
(3,116
)
(2,398
)
(7,157
)
(5,904
)
Net cash provided by (used in) financing activities
(95,155
)
23,562
3,364
59,498
Effect of exchange rate changes
(2,223
)
(2,531
)
2,095
(6,176
)
Net increase (decrease) in cash and cash equivalents
220,378
(3,281
)
(381,003
)
(240,946
)
Cash and cash equivalents, beginning of period
409,925
246,169
1,011,306
483,834
Cash and cash equivalents, end of period
$
630,303
$
242,888
$
630,303
$
242,888
Supplemental cash flow disclosure:
Cash paid (received) during the period for:
Interest
$
1,378
$
292
$
3,980
$
793
Income taxes, net of tax refunds
$
4,260
$
6,446
$
(530
)
$
27,520
Non
-
cash financing and investing activities
Fixed assets acquired under capital leases
$
6,765
$
3,105
$
12,929
$
17,897

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements
1. Summary of Business and Significant Accounting Policies
Description of Business
Salesforce.com, inc. (the “Company”) is a leading provider of enterprise cloud computing applications. The Company provides a
comprehensive customer and collaboration relationship management (“CRM”) service to businesses of all sizes and industries worldwide and
provides a technology platform for customers and developers to build and run applications. The Company offers its services on a subscription
basis.
Fiscal Year
The Company’s fiscal year ends on January 31. References to fiscal 2011, for example, refer to the fiscal year ending January 31, 2011.
Basis of Presentation
The accompanying condensed consolidated balance sheet as of October 31, 2010 and the condensed consolidated statements of operations
and the condensed consolidated statements of cash flows for the three and nine months ended October 31, 2010 and 2009, respectively, are
unaudited. The condensed consolidated balance sheet data as of January 31, 2010 was derived from the audited consolidated financial statements
which are included in the Company’s Form 10-K for the fiscal year ended January 31, 2010, which was filed with the Securities and Exchange
Commission (the “SEC”) on March 11, 2010. The accompanying statements should be read in conjunction with the audited consolidated
financial statements and related notes contained in the Company’s fiscal 2010 Form 10-K.
The accompanying condensed consolidated financial statements have been prepared in accordance with U.S. generally accepted accounting
principles, or U.S. GAAP, for interim financial information and with the instructions to Form 10-Q and Article 10 of Regulation S-X.
Accordingly, they do not include all of the financial information and footnotes required by U.S. GAAP for complete financial statements. In the
opinion of the Company’s management, the unaudited condensed consolidated financial statements have been prepared on the same basis as the
audited consolidated financial statements in the Form 10-K, and include all adjustments necessary for the fair presentation of the Company’s
statement of financial position as of October 31, 2010, and its results of operations and its cash flows for the three and nine months ended
October 31, 2010 and 2009. All adjustments are of a normal recurring nature. The results for the three and nine months ended October 31, 2010
are not necessarily indicative of the results to be expected for any subsequent quarter or for the fiscal year ending January 31, 2011.
Use of Estimates
The preparation of financial statements in conformity with U.S. GAAP requires management to make estimates and assumptions in the
Company’s consolidated financial statements and notes thereto.
Significant estimates and assumptions made by management include the determination of the provision for income taxes, whether an other-
than-temporary decline has occurred in the fair value of certain investments in marketable securities and investments in privately-held
companies, the fair value of stock awards issued and the allocation of the preliminary purchase consideration for the acquisition of businesses.
Actual results could differ from those estimates.
Principles of Consolidation
The consolidated financial statements include the accounts of the Company and its wholly owned subsidiaries. All significant
intercompany balances and transactions have been eliminated in consolidation.
6

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Additionally, the Company holds a controlling interest in Kabushiki Kaisha salesforce.com (“Salesforce Japan”). During the three months
ended October 31, 2010, the Company increased its ownership interest in Salesforce Japan from 73 percent to 96 percent (see Note 5).
Given the Company’s controlling interest in Salesforce Japan, the accounts of Salesforce Japan have been consolidated with the accounts
of the Company, and a noncontrolling interest has been recorded for the noncontrolling investors’ interests in the net assets and operations of
Salesforce Japan to the extent of noncontrolling investors’ individual investments.
Segments
The Company operates in one segment.
Foreign Currency Translation
The functional currency of the Company’s major foreign subsidiaries is generally the local currency. Adjustments resulting from
translating foreign functional currency financial statements into U.S. dollars are recorded as part of a separate component of stockholders’
equity. Foreign currency transaction gains and losses are included in net income. All assets and liabilities denominated in a foreign currency are
translated into U.S. dollars at the exchange rate on the balance sheet date. Revenues and expenses are translated at the average exchange rate
during the period. Equity transactions are translated using historical exchange rates.
Concentrations of Credit Risk and Significant Customers
The Company’s financial instruments that are exposed to concentrations of credit risk consist primarily of cash and cash equivalents,
marketable securities and trade accounts receivable. Although the Company deposits its cash with multiple financial institutions, its deposits, at
times, may exceed federally insured limits. Collateral is not required for accounts receivable. The Company maintains an allowance for doubtful
accounts receivable balances. The allowance is based upon historical loss patterns, the number of days that billings are past due and an
evaluation of the potential risk of loss associated with delinquent accounts.
No customer accounted for more than 5 percent of accounts receivable at October 31, 2010 and January 31, 2010. No single customer
accounted for 5 percent or more of total revenue in the three and nine months ended October 31, 2010 and 2009, respectively.
As of October 31, 2010 and January 31, 2010, assets located outside the Americas were 15 percent and 12 percent of total assets,
respectively.
Revenues by geographical region are as follows (in thousands):
7
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Americas
$
292,540
$
232,802
$
826,493
$
679,460
Europe
76,464
60,761
208,851
168,355
Asia Pacific
60,083
36,986
164,928
103,719
$
429,087
$
330,549
$
1,200,272
$
951,534

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Cash and Cash Equivalents
The Company considers all highly liquid investments purchased with an original maturity of three months or less to be cash equivalents.
Cash and cash equivalents are stated at fair value.
Marketable Securities
Management determines the appropriate classification of investments in marketable securities at the time of purchase and reevaluates such
determination at each balance sheet date. Securities are classified as available for sale and are carried at fair value, with the unrealized gains and
losses, net of tax, reported as a separate component of stockholders’ equity. Fair value is determined based on quoted market rates when
observable or utilizing data points that are observable, such as quoted prices, interest rates and yield curves. Declines in fair value judged to be
other-than-temporary on securities available for sale are included as a component of investment income. The cost of securities sold is based on
the specific-identification method. Interest on securities classified as available for sale is also included as a component of investment income. In
order to determine whether a decline in value is other-than-
temporary, we evaluate, among other factors: the duration and extent to which the fair
value has been less than the carrying value, our financial condition and business outlook, including key operational and cash flow metrics,
current market conditions and our intent and ability to retain the investment for a period of time sufficient to allow for any anticipated recovery
in fair market value.
Fair Value Measurement
The Company reports its financial and non-financial assets and liabilities that are re-measured and reported at fair value at each reporting
period. The Company measures its cash equivalents, marketable securities, foreign currency derivative contracts and contingent considerations
related to acquisitions at fair value. All of the Company’s cash equivalents, marketable securities and foreign currency derivative contracts are
classified within Level 1 or Level 2, which are described below. This is because the Company’s cash equivalents and marketable securities are
valued using quoted market prices or alternative pricing sources and models utilizing market observable inputs.
The Company established a three-tier value hierarchy, which prioritizes the inputs used in the valuation methodologies in measuring fair
value:
8
Level 1.
Observable inputs that reflect quoted prices (unadjusted) for identical assets or liabilities in active markets.
Level 2.
Include other inputs that are directly or indirectly observable in the marketplace.
Level 3.
Unobservable inputs which are supported by little or no market activity.

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
The following table presents information about the Company’s assets and liabilities that are measured at fair value as of October 31, 2010
and indicates the fair value hierarchy of the valuation (in thousands):
9
Description
Quoted Prices in
Active Markets
for Identical Assets
(Level 1)
Significant Other
Observable
Inputs
(Level 2)
Significant
Unobservable
Inputs
(Level 3)
Balance as of
October 31, 2010
Cash equivalents (1):
Time deposits
$
26,068
$
—
$
—
$
26,068
Money market mutual funds
91,636
—
—
91,636
Marketable securities:
Corporate notes and obligations
—
812,443
—
812,443
Government obligations
3,277
—
—
3,277
U.S. treasury securities
25,622
—
—
25,622
U.S. agency obligations
—
122,210
—
122,210
Mortgage backed securities
—
60,006
—
60,006
Collateralized mortgage obligations
—
126,640
—
126,640
Municipal securities
—
19,629
—
19,629
Marketable equity securities
2,310
—
—
2,310
Foreign currency derivative contracts (2)
—
575
—
575
Total Assets
$
148,913
$
1,141,503
$
—
$
1,290,416
Liabilities
Foreign currency derivative contracts (3)
$
—
$
627
$
—
$
627
Contingent considerations (related to acquisitions)
(3)
—
—
16,820
16,820
Total Liabilites
$
—
$
627
$
16,820
$
17,447
(1) Included in “cash and cash equivalents” in the accompanying Condensed Consolidated Balance Sheet as of October 31, 2010, in addition
to $512.6 million of cash.
(2) Included in “prepaid expenses and other current assets” in the accompanying Condensed Consolidated Balance Sheet as of October 31,
2010.
(3)
Included in
“
accrued expenses and other current liabilities
”
in the accompanying Condensed Consolidated Balance Sheet as of October 31,
2010.

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
The following table presents information about the Company’s assets and liabilities that are measured at fair value on a recurring basis as
of January 31, 2010 and indicates the fair value hierarchy of the valuation (in thousands):
Derivative Financial Instruments
The Company enters into foreign currency derivative contracts with financial institutions to reduce the risk that its cash flows and earnings
will be adversely affected by foreign currency exchange rate fluctuations. The Company uses foreign currency derivative contracts to minimize
the Company’s exposure of balances denominated in Euros, Canadian dollar, Swiss francs, Australian dollars, Singapore dollars, Japanese yen
and British pound sterlings. The Company’s program is not designated for trading or speculative purposes. As of October 31, 2010 and
January 31, 2010 the foreign currency derivative contracts that were not settled are recorded at fair value on the condensed consolidated balance
sheet.
The Company’
s foreign currency derivative contracts which are not designated as hedging instruments are used to reduce the exchange rate
risk associated primarily with intercompany receivables and payables. Foreign currency derivative contracts are marked-to-market at the end of
each reporting period with gains and losses recognized as other income (expense) to offset the gains or losses resulting from the settlement or
remeasurement of the underlying foreign currency denominated receivables and payables. While the contract or notional amount is often used to
express the volume of foreign currency derivative contracts, the amounts potentially subject to
10
Description
Quoted Prices in
Active Markets
for Identical Assets
(Level 1)
Significant Other
Observable
Inputs
(Level 2)
Significant
Unobservable
Inputs
(Level 3)
Balance as of
January 31, 2010
Cash equivalents (1):
Time deposits
$
11,410
$
—
$
—
$
11,410
Money market mutual funds
123,868
—
—
123,868
U.S. treasury securities
399,140
—
—
399,140
U.S. agency obligations
—
364,197
—
364,197
Marketable securities:
Corporate notes and obligations
—
337,574
—
337,574
U.S. agency obligations
—
163,455
—
163,455
U.S. treasury securities
136,660
—
136,660
Mortgage backed securities
—
40,865
—
40,865
Collateralized mortgage obligations
—
37,188
—
37,188
Foreign currency derivative contracts (2)
—
1,593
—
1,593
Total Assets
$
671,078
$
944,872
$
—
$
1,615,950
Liabilities
Foreign currency derivative contracts (3)
$
—
$
402
$
—
$
402
Total Liabilities
$
—
$
402
$
—
$
402
(1) Included in “cash and cash equivalents”
in the accompanying Condensed Consolidated Balance Sheet as of January 31, 2010, in addition to
$112.7 million of cash.
(2)
Included in
“
prepaid expenses and other current assets
”
in the accompanying Condensed Consolidated Balance Sheet as of January 31,
2010.
(3)
Included in
“
accrued expenses and other current liabilities
”
in the accompanying Condensed Consolidated Balance Sheet as of January 31,
2010.

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
credit risk are generally limited to the amounts, if any, by which the counterparties’ obligations under the agreements exceed the obligations of
the Company to the counterparties.
Details on outstanding foreign currency derivative contracts related primarily to intercompany receivables and payables are presented
below (in thousands):
The fair value of outstanding derivative instruments is summarized below (in thousands):
The effect of the derivative instruments not designated as hedging instruments on the Condensed Statements of Operations for the three
and nine months ended October 31, 2010 and October 31, 2009, respectively are summarized below (in thousands):
11
October 31,
2010
January 31,
2010
Notional amount of foreign currency derivative contracts
$
157,049
$
74,705
Fair value of foreign currency derivative contracts
(52
)
1,191
Balance Sheet Location
Fair Value of Derivative Instruments
As of October 31,
2010
As of January 31,
2010
Derivative Assets
Derivatives not designated as hedging instruments:
Foreign currency derivative contracts
Prepaid expenses and
other current assets
$
575
$
1,593
Derivative Liabilities
Derivatives not designated as hedging instruments:
Foreign currency derivative contracts
Accrued expenses and
other current liabilities
$
627
$
402
Derivatives Not Designated as Hedging
Instruments
Gains (Losses) Recognized in Income on
Derivative Instruments
Location
Three months ended
October 31,
2010
2009
Foreign currency derivative contracts
Other expense
$
(52
)
$
513
Derivatives Not Designated as Hedging
Instruments
Losses Recognized in Income on
Derivative Instruments
Location
Nine months ended
October 31,
2010
2009
Foreign currency derivative contracts
Other expense
$
(1,057
)
$
(151
)

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Investment Income
Investment income consists of interest income, realized gains, and realized losses on the Company’
s cash, cash equivalents and marketable
securities.
The components of investment income are presented below (in thousands):
Interest Expense
Interest expense consists of interest on the Company’s capital lease commitments and convertible senior notes. As described in Note 2, in
accounting for the senior notes at the time of issuance in January 2010, the par value of the senior notes was allocated between liabilities and
equity. The portion allocated to liabilities was based upon an imputed, nonconvertible debt market interest rate of 5.86 percent. The allocation
created an imputed debt discount of approximately $125.0 million which is being accreted to interest expense over the 5 year term of the senior
notes using the effective interest rate. The 5.86 percent imputed interest rate includes the contractual interest rate of 0.75 percent.
Comprehensive Income
Comprehensive income consists of net income and other comprehensive income (loss), which includes certain changes in equity that are
excluded from net income. Specifically, cumulative foreign currency translation adjustments and unrealized gains and losses on marketable
securities, net of tax, are included in accumulated other comprehensive gain (loss). Comprehensive income has been reflected in stockholders’
equity.
Comprehensive income consisted of the following (in thousands):
The components of accumulated other comprehensive gain (loss) were as follows (in thousands):
12
Three months
ended October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Interest income
$
8,447
$
5,821
$
21,597
$
16,173
Realized gains
4,333
1,951
8,986
5,137
Realized losses
(1,081
)
(269
)
(2,274
)
(1,530
)
Total investment income
$
11,699
$
7,503
$
28,309
$
19,780
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Consolidated net income
$
22,368
$
21,443
$
58,827
$
62,277
Less: net income attributable to noncontrolling interest
(1,296
)
(752
)
(5,266
)
(1,952
)
Translation and other adjustments
(2,299
)
(2,947
)
3,698
(6,532
)
Unrealized gain on marketable securities
3,474
1,724
6,762
6,198
Comprehensive income attributable to salesforce.com
$
22,247
$
19,468
$
64,021
$
59,991
October 31,
2010
January 31,
2010
Foreign currency translation and other adjustments
$
(3,368
)
$
(7,066
)
Net unrealized gain on marketable securities and cash equivalents
12,398
5,636
$
9,030
$
(1,430
)

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Net Income Per Share
Basic net income per share attributable to salesforce.com is computed by dividing net income attributable to salesforce.com by the
weighted-average number of common shares outstanding for the fiscal period. Diluted net income per share attributable to salesforce.com is
computed giving effect to all potential dilutive common stock, including options, restricted stock units, warrants and the convertible senior notes.
The dilutive effect of outstanding awards is reflected in diluted earnings per share by application of the treasury stock method.
A reconciliation of the denominator used in the calculation of basic and diluted net income per share attributable to salesforce.com is as
follows (in thousands):
The following were excluded from the computation of diluted shares outstanding as they would have had an anti-dilutive impact. The
dilutive securities are excluded when, for example, their exercise prices, unrecognized compensation and tax benefits are greater than the
average fair values of the Company’s common stock (in thousands).
Income Taxes
The Company uses the liability method of accounting for income taxes. Under this method, deferred tax assets and liabilities are
determined based on temporary differences between the financial statement and tax basis of assets and liabilities and net operating loss and credit
carryforwards using enacted tax rates in effect for the year in which the differences are expected to reverse. The effect on deferred tax assets and
liabilities of a change in tax rates is recognized in income in the period that includes the enactment date. Valuation allowances are established
when necessary to reduce deferred tax assets to the amounts more likely than not expected to be realized.
The total income tax benefit recognized in the accompanying condensed consolidated statements of operations related to stock-based
compensation was $28.7 million and $22.8 million for the nine months ended October 31, 2010 and 2009 respectively.
13
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Numerator:
Net income attributable to salesforce.com
$
21,072
$
20,691
$
53,561
$
60,325
Denominator:
Weighted
-
average shares outstanding for basic earnings per share
130,888
124,561
129,461
123,871
Effect of dilutive securities:
0.75% convertible senior notes
1,513
—
993
—
Employee stock awards
4,643
4,035
4,553
3,122
Adjusted weighted
-
average shares outstanding and assumed conversions for
diluted earnings per share
137,044
128,596
135,007
126,993
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Stock awards
164
3,751
514
4,611
Warrants
6,736
—
6,736
—

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Effective Tax Rate
The Company computes its provision for income taxes by applying the estimated annual effective tax rate to income from recurring
operations and adjusts the provision for discrete tax items recorded in the period. The Company’s effective tax rate of 41 percent for the nine
months ended October 31, 2010 was higher than the federal statutory rate of 35 percent primarily due to state income taxes, foreign tax rate
differential, non-deductible expenses as a result of acquisitions and the unfavorable impact of a change in California tax law, which were
partially offset by California tax credits. Similarly, the Company’s effective tax rate of 42 percent for the nine months ended October 31, 2009
was higher than the federal statutory rate of 35 percent primarily due to state income taxes, foreign tax rate differential and the unfavorable
impact of a change in California tax law, which were partially offset by federal and California tax credits.
Unrecognized Tax Benefits and Other Considerations
The Company records liabilities related to its uncertain tax positions. During the nine months ended October 31, 2010, the Company
recorded a discrete favorable tax item relating to certain decreases in unrecognized tax benefits as a result of a favorable court ruling in transfer
pricing matters and lapsing of the statutes of limitations.
The Company’s existing tax positions will continue to generate an increase in tax liabilities or unrecognized tax benefits. The Company
does not believe that it is reasonably possible that there will be a significant increase or decrease in unrecognized tax benefits over the next
twelve months. However, an adverse resolution of one or more uncertain tax positions in any period could have a material impact on the results
of operations for that period.
Tax positions for the Company and its subsidiaries are subject to income tax audits by multiple tax jurisdictions throughout the world.
During the quarter ended October 31, 2010, the National Tax Agency of Japan completed the examination of the Company’s fiscal 2010 tax
return for Japan. No material adjustment was made as a result of the examination.
Revenue Recognition
The Company derives its revenues from two sources: (1) subscription revenues, which are comprised of subscription fees from customers
accessing its enterprise cloud computing application service, and from customers purchasing additional support beyond the standard support that
is included in the basic subscription fee; and (2) related professional services and other revenue. “Other revenue” consists primarily of training
fees. The Company recognizes revenue when all of the following conditions are met:
The Company’s arrangements do not contain general rights of return.
Subscription and support revenues are recognized ratably over the contract terms beginning on the commencement date of each contract.
Amounts that have been invoiced are recorded in accounts receivable and in deferred revenue or revenue, depending on whether the revenue
recognition criteria have been met.
14
•
There is persuasive evidence of an arrangement;
•
The service has been provided to the customer;
•
The collection of the fees is reasonably assured; and
•
The amount of fees to be paid by the customer is fixed or determinable.

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Professional services and other revenues, when sold with subscription and support offerings, are accounted for separately when these
services have value to the customer on a standalone basis and there is objective and reliable evidence of fair value of each deliverable. When
accounted for separately, revenues are recognized as the services are rendered for time and material contracts, and when the milestones are
achieved and accepted by the customer for fixed price contracts. The majority of the Company’s consulting contracts are on a time and materials
basis. Training revenues are recognized after the services are performed. For revenue arrangements with multiple deliverables, such as an
arrangement that includes subscription, premium support, consulting or training services, the Company allocates the total amount the customer
will pay to the separate units of accounting based on their relative fair values, as determined by the price of the undelivered items when sold
separately.
In determining whether the consulting services can be accounted for separately from subscription and support revenues, the Company
considers the following factors for each consulting agreement: availability of the consulting services from other vendors, whether objective and
reliable evidence for fair value exists for the undelivered elements, the nature of the consulting services, the timing of when the consulting
contract was signed in comparison to the subscription service start date, and the contractual dependence of the subscription service on the
customer’s satisfaction with the consulting work. If a consulting arrangement does not qualify for separate accounting, the Company recognizes
the consulting revenue ratably over the remaining term of the subscription contract. Additionally, in these situations, the Company defers only
the direct costs of the consulting arrangement and amortizes those costs over the same time period as the consulting revenue is recognized. As of
October 31, 2010 and January 31, 2010, the deferred cost on the accompanying condensed consolidated balance sheet totaled $27.8 million and
$19.1 million, respectively. These deferred costs are included in prepaid expenses and other current assets and other assets.
Deferred Revenue
Deferred revenue primarily consists of billings or payments received in advance of revenue recognition from the Company’s subscription
service described above and is recognized as the revenue recognition criteria are met. The Company generally invoices its customers in annual or
quarterly installments. Accordingly, the deferred revenue balance does not represent the total contract value of annual or multi-year, non-
cancelable subscription agreements. Deferred revenue also includes certain deferred professional services fees which are recognized as revenue
ratably over the subscription contract term. The Company defers the professional service fees in situations where the professional services and
subscription contracts are accounted for as a single unit of accounting. Deferred revenue that will be recognized during the succeeding 12-month
period is recorded as current deferred revenue and the remaining portion is recorded as noncurrent. Approximately 8 percent and 6 percent of
total deferred revenue as of October 31, 2010 and January 31, 2010, respectively related to deferred professional services revenue.
Deferred Commissions
Deferred commissions are the incremental costs that are directly associated with non-cancelable subscription contracts with customers and
consist of sales commissions paid to the Company’s direct sales force. The commissions are deferred and amortized over the non-cancelable
terms of the related customer contracts, which are typically 12 to 24 months. The commission payments are paid in full the month after the
customer’s service commences. The deferred commission amounts are recoverable through the future revenue streams under the non-cancelable
customer contracts. The Company believes this is the preferable method of accounting as the commission charges are so closely related to the
revenue from the non-cancelable customer contracts that they should be recorded as an asset and charged to expense over the same period that
the subscription revenue is recognized. Amortization of deferred commissions is included in marketing and sales expense in the accompanying
condensed consolidated statements of operations.
15

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Accounting for Stock-Based Compensation
The Company recognizes share-based expenses on a straight-line over the requisite service period of the awards, which is the vesting term
of four years. Stock-based expenses are recognized net of estimated forfeiture activity.
The fair value of each option grant was estimated on the date of grant using the Black-Scholes option pricing model with the following
assumptions and fair value per share:
Since November 2009, the weighted-average estimated life was based on an actual analysis of expected life. Prior to November 2009, the
weighted-average estimated life assumption of 4 years was based on the average of the vesting term and the 5 year contractual lives of options
awarded. The weighted average risk free interest rate is based on the rate for a 4 year U.S. government security at the time of the option grant.
The Company estimated its future stock price volatility considering both its observed option-implied volatilities and its historical volatility
calculations. Management believes this is the best estimate of the expected volatility over the 4 year weighted-average expected life of its option
grants.
During the three months ended October 31, 2010 and 2009, the Company capitalized $0.8 million and $1.0 million, respectively, of stock
based expenses related to capitalized internal-use software development and deferred professional services costs and capitalized $2.1 million for
each of the nine months ended October 31, 2010 and 2009.
During the nine months ended October 31, 2010, the Company recognized stock-based expense of $78.7 million. As of October 31, 2010,
the aggregate stock compensation remaining to be amortized to costs and expenses was $237.7 million. The Company expects this stock
compensation balance to be amortized as follows: $29.3 million during the remaining three months of fiscal 2011; $101.4 million during fiscal
2012; $64.7 million during fiscal 2013; $38.2 million during fiscal 2014 and $4.1 million during fiscal 2015. The expected amortization reflects
only outstanding stock awards as of October 31, 2010 and assumes no forfeiture activity. The Company expects to continue to issue share-based
awards to its employees in future periods.
Goodwill, Intangible Assets and Impairment Assessments
Goodwill represents the excess of the purchase price of an acquired business over the fair value of the underlying net tangible and
intangible assets. The goodwill balance is assigned to a reporting unit which is generally the consolidated group. Goodwill is tested for
impairment at least annually (more frequently if certain indicators are present). In the event that the Company determines that the carrying value
of goodwill is less than fair value, the Company will incur an impairment charge for the amount of the difference during the quarter in which the
determination is made.
Intangible assets are amortized over their useful lives. Each period the Company evaluates the estimated remaining useful life of its
intangible assets and whether events or changes in circumstances warrant a revision to
16
Three months ended
October 31,
Nine months ended October 31,
2010
2009
2010
2009
Volatility
45
–
50
%
52
%
45
–
50
%
52
–
60
%
Weighted
-
average estimated life
3.8 years
4 years
3.8 years
4 years
Weighted
-
average risk
-
free interest rate
0.98
–
1.08
%
2.16
–
2.26
%
0.98
–
2.11
%
1.78
–
2.39
%
Dividend yield
—
—
—
—
Weighted
-
average fair value per share of grants
$
40.89
$
23.03
$
31.36
$
20.24

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
the remaining period of amortization. The carrying amounts of these assets are periodically reviewed for impairment whenever events or changes
in circumstances indicate that the carrying value of these assets may not be recoverable. Recoverability of these assets is measured by
comparison of the carrying amount of each asset to the future undiscounted cash flows the asset is expected to generate. In the event that the
Company determines certain assets are not fully recoverable, the Company will incur an impairment charge for those assets or portion thereof
during the quarter in which the determination is made.
Warranties and Indemnification
The Company’s enterprise cloud computing application service is typically warranted to perform in a manner consistent with general
industry standards that are reasonably applicable and materially in accordance with the Company’s online help documentation under normal use
and circumstances.
The Company’s arrangements generally include certain provisions for indemnifying customers against liabilities if its products or services
infringe a third-party’s intellectual property rights. To date, the Company has not incurred any material costs as a result of such indemnifications
and has not accrued any liabilities related to such obligations in the accompanying condensed consolidated financial statements.
The Company has also agreed to indemnify its directors and executive officers for costs associated with any fees, expenses, judgments,
fines and settlement amounts incurred by any of these persons in any action or proceeding to which any of those persons is, or is threatened to
be, made a party by reason of the person’s service as a director or officer, including any action by the Company, arising out of that person’s
services as the Company’s director or officer or that person’s services provided to any other company or enterprise at the Company’s request.
The Company maintains director and officer insurance coverage that would generally enable the Company to recover a portion of any future
amounts paid. The Company may also be subject to indemnification obligations by law with respect to the actions of its employees under certain
circumstances and in certain jurisdictions.
New Accounting Pronouncement
In September 2009, the FASB issued Accounting Standards Update No. 2009-13, “Multiple-Deliverable Revenue Arrangements—a
consensus of the FASB Emerging Issues Task Force” (ASU 2009-13). It updates the existing multiple-element revenue arrangements guidance
currently included under ASC 605-25, which originated primarily from the guidance in EITF Issue No. 00-21, “Revenue Arrangements with
Multiple Deliverables” (EITF 00-21). The revised guidance primarily provides two significant changes: 1) eliminates the need for objective and
reliable evidence of the fair value for the undelivered element in order for a delivered item to be treated as a separate unit of accounting, and 2)
eliminates the residual method to allocate the arrangement consideration. In addition, the guidance also expands the disclosure requirements for
revenue recognition. ASU 2009-13 will be effective for the first annual reporting period beginning on or after June 15, 2010. The Company
believes the future impact of this new accounting pronouncement will not be material to consolidated net income.
Subsequent Events
The Company evaluated subsequent events through the date this Quarterly Report on Form 10-Q was filed with the SEC.
On November 1, 2010, the Company completed the purchase of approximately 14 acres of undeveloped land in San Francisco, California,
including entitlements and improvements associated with the land and parking rights in an existing garage for approximately $278.0 million in
cash. The Company has not set a date for construction yet, but the Company plans to use the land to build a facility that will become its new
global headquarters.
17

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
2. Balance Sheet Accounts
Marketable Securities
At October 31, 2010, marketable securities consisted of the following (in thousands):
At January 31, 2010, marketable securities consisted of the following (in thousands):
As of October 31, 2010, the following investments were in an unrealized loss position (in thousands):
18
Amortized
Cost
Unrealized
Gains
Unrealized
Losses
Fair Value
Corporate notes and obligations
$
796,870
$
15,839
$
(266
)
$
812,443
U.S. agency obligations
121,683
530
(3
)
122,210
U.S. treasury securities
25,488
134
—
25,622
Collateralized mortgage obligations
124,691
2,092
(143
)
126,640
Mortgage backed securities
59,535
881
(410
)
60,006
Government obligations
3,203
74
—
3,277
Municipal securities
19,596
94
(61
)
19,629
Marketable equity securities
785
1,525
—
2,310
$
1,151,851
$
21,169
$
(883
)
$
1,172,137
Amortized
Cost
Unrealized
Gains
Unrealized
Losses
Fair Value
Corporate notes and obligations
$
329,750
$
7,889
$
(65
)
$
337,574
U.S. treasury securities
136,606
170
(116
)
136,660
Mortgage backed securities
40,187
719
(41
)
40,865
Collateralized mortgage obligations
36,785
436
(33
)
37,188
U.S. agency obligations
162,896
571
(12
)
163,455
$
706,224
$
9,785
$
(267
)
$
715,742
October 31,
2010
January 31,
2010
Recorded as follows (in thousands):
Short
-
term (due in one year or less)
$
139,545
$
230,659
Long
-
term
1,032,592
485,083
$
1,172,137
$
715,742
Less than 12 Months
12 Months or Greater
Total
Fair
Value
Unrealized
Losses
Fair
Value
Unrealized
Losses
Fair Value
Unrealized
Losses
Corporate notes and obligations
$
63,150
$
(257
)
$
398
$
(9
)
$
63,548
$
(266
)
Collateralized mortgage obligations
28,825
(143
)
—
—
28,825
(143
)
Mortgage backed securities
26,877
(410
)
—
—
26,877
(410
)
U.S. agency obligations
14,004
(3
)
—
—
14,004
(3
)
Municipal securities
4,130
(61
)
—
—
4,130
(61
)
$
136,986
$
(874
)
$
398
$
(9
)
$
137,384
$
(883
)

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
The unrealized loss for each of these fixed rate marketable securities ranged from less than $1,000 to $109,000. The Company does not
believe any of the unrealized losses represent an other-than-temporary impairment based on its evaluation of available evidence as of
October 31, 2010. The Company expects to receive the full principal and interest on all of these marketable securities.
Prepaid Expenses and Other Current Assets
Prepaid expenses and other current assets consisted of the following (in thousands):
Fixed Assets
Fixed assets consisted of the following (in thousands):
Depreciation and amortization expense totaled $11.0 million and $8.4 million for the three months ended October 31, 2010 and 2009,
respectively, and $28.9 million and $22.5 million for the nine months ended October 31, 2010 and 2009, respectively.
Fixed assets at October 31, 2010 and January 31, 2010 included $38.2 million and $27.1 million, respectively, acquired under capital lease
agreements. Accumulated amortization relating to equipment and software under capital leases totaled $15.7 million and $11.0 million at
October 31, 2010 and January 31, 2010, respectively. Amortization of assets under capital leases is included in depreciation and amortization
expense.
Capitalized Software
Capitalized software consisted of the following (in thousands):
19
October 31,
2010
January 31,
2010
Deferred professional services costs
$
17,415
$
13,420
Prepaid expenses and other current assets
46,928
42,314
$
64,343
$
55,734
October 31,
2010
January 31,
2010
Computers, equipment and software
$
104,773
$
87,608
Furniture and fixtures
18,535
17,325
Leasehold improvements
88,054
71,882
211,362
176,815
Less accumulated depreciation and amortization
(95,284
)
(87,104
)
$
116,078
$
89,711
October 31,
2010
January 31,
2010
Capitalized internal-
use software development costs, net of accumulated amortization of $30,929
and $21,392, respectively
$
27,931
$
22,675
Acquired developed technology, net of accumulated amortization of $31,383 and $20,932,
respectively
51,568
12,134
$
79,499
$
34,809

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Capitalized internal use software amortization expense totaled $3.3 million and $2.5 million for the three months ended October 31, 2010
and 2009, respectively. Acquired developed technology amortization expense for the three months ended October 31, 2010 and 2009, was $4.9
million and $2.0 million, respectively. Capitalized internal use software amortization expense totaled $9.5 million and $7.0 million for the nine
months ended October 31, 2010 and 2009, respectively. Acquired developed technology amortization expense for the nine months ended
October 31, 2010 and 2009 was $10.4 million and $5.7 million, respectively.
Other Assets, net
Other assets consisted of the following (in thousands):
Purchased intangible assets amortization expense for the three months ended October 31, 2010 and 2009, was $1.0 million and $0.8
million, respectively and for the nine months ended October 31, 2010 and 2009 was $3.0 million and $2.4 million, respectively.
In October 2010, the Company paid a third party escrow agent $8.0 million as a deposit for the purchase of undeveloped land, parking
rights in an existing garage, and other entitlements and improvements associated with the land. On November 1, 2010 the Company purchased
this undeveloped land of which this $8.0 million was part of those proceeds (see Note 1).
Goodwill
Goodwill represents the excess of the purchase consideration in a business combination over the fair value of net tangible and intangible
assets acquired. Goodwill amounts are not amortized, but rather tested for impairment at least annually during the fourth quarter. There was no
impairment of goodwill for the nine months ended October 31, 2010.
Goodwill consisted of the following (in thousands):
20
October 31,
2010
January 31,
2010
Deferred professional services costs, noncurrent portion
$
10,347
$
5,639
Long
-
term deposits
12,372
11,084
Deposit related to land purchase
8,000
—
Purchased intangible assets, net of accumulated amortization of $8,721 and $5,694, respectively
8,716
6,613
Acquired patents and domain names, net of accumulated amortization of $467 and $121,
respectively
4,153
133
Investments in privately
-
held companies
10,678
6,288
Other
14,928
10,008
$
69,194
$
39,765
Total
Balance as of January 31, 2010
$
48,955
Jigsaw Data Corporation
133,254
Other acquisition activity
4,829
Balance as of October 31, 2010
$
187,038

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
In the third quarter of fiscal 2011, the Company acquired a privately-held company for $3.8 million in cash. The Company accounted for
this transaction as a business combination. Of the $3.8 million purchase price, the Company allocated $1.9 million to acquired developed
technology with a useful life of 3 years and the remainder to goodwill.
Accrued Expenses and Other Current Liabilities
Accrued expenses and other current liabilities consisted of the following (in thousands):
0.75% Convertible Senior Notes
In January 2010, the Company issued at par value $575.0 million of 0.75% convertible senior notes due January 15, 2015 (the “Notes”).
Interest is payable semi-annually in arrears on January 15 and July 15 of each year, commencing July 15, 2010.
The Notes are governed by an Indenture dated as of January 19, 2010, between the Company, as issuer, and U.S. Bank National
Association, as trustee. The Notes do not contain any financial covenants or any restrictions on the payment of dividends, the incurrence of
senior debt or other indebtedness, or the issuance or repurchase of securities by the Company. The Notes are unsecured and rank senior in right
of payment to the Company’s future indebtedness that is expressly subordinated in right of payment to the Notes and rank equal in right of
payment to the Company’s existing and future unsecured indebtedness that is not so subordinated and are effectively subordinated in right of
payment to any of the Company’s cash equal to the principal amount of the Notes, and secured indebtedness to the extent of the value of the
assets securing such indebtedness and are structurally subordinated to all existing and future indebtedness and liabilities incurred by our
subsidiaries, including trade payables.
If converted, holders will receive cash equal to the principal amount of the Notes, and at the Company’s election, cash and/or shares of the
Company’s common stock for any amounts in excess of the principal amounts.
The initial conversion rate is 11.7147 shares of common stock per $1,000 principal amount of Notes, subject to anti-dilution adjustments.
The initial conversion price is approximately $85.36 per share of common stock. Throughout the term of the Notes, the conversion rate may be
adjusted upon the occurrence of certain events, including for any cash dividends. Holders of the Notes will not receive any cash payment
representing accrued and unpaid interest upon conversion of a Note. Accrued but unpaid interest will be deemed to be paid in full upon
conversion rather than cancelled, extinguished or forfeited. Holders may convert their Notes under the following circumstances:
21
October 31,
2010
January 31,
2010
Accrued compensation
$
104,919
$
90,223
Accrued other liabilities
114,134
46,188
Accrued other taxes payable
30,885
27,757
Accrued professional costs
15,837
10,740
Accrued rent
21,852
19,830
$
287,627
$
194,738
•
during any fiscal quarter commencing after April 30, 2010, if, for at least 20 trading days during the 30 consecutive trading day period
ending on the last trading day of the immediately preceding fiscal quarter, the last reported sales price of the Company’s common
stock for such trading day is greater than or equal to 130 percent of the applicable conversion price on such trading day share of
common stock on such last trading day;

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
As of October 31, 2010, the Notes are not yet convertible up to 6.7 million shares of the Company’s common stock.
Holders of the Notes have the right to require the Company to purchase with cash all or a portion of the Notes upon the occurrence of a
fundamental change, such as a change of control at a purchase price equal to 100 percent of the principal amount of the Notes plus accrued and
unpaid interest. In certain circumstances, following certain corporate transactions that constitute a change of control, the Company will increase
the conversion rate for a holder who elects to convert the Notes in connection with such change of control.
In accounting for the issuance of the Notes, the Company separated the Notes into liability and equity components. The carrying amount of
the liability component was calculated by measuring the fair value of a similar liability that does not have an associated convertible feature. The
carrying amount of the equity component representing the conversion option was determined by deducting the fair value of the liability
component from the par value of the Notes as a whole. The excess of the principal amount of the liability component over its carrying amount
(“debt discount”) is amortized to interest expense over the term of the Note. The equity component is not remeasured as long as it continues to
meet the conditions for equity classification.
In accounting for the transaction costs related to the Note issuance, the Company allocated the total amount incurred to the liability and
equity components. Transaction costs attributable to the liability component are being amortized to expense over the term of the Notes, and
transaction costs attributable to the equity component were netted with the equity component in additional paid-in capital. Debt issuance costs,
net of amortization, were $5.6 million as of October 31, 2010 and equity issuance costs were $1.8 million. Additionally, the Company in January
2010 recorded a deferred tax liability of $51.1 million in connection with the Notes. The Notes consisted of the following (in thousands):
amortized over the remaining life of the Notes using the effective interest rate method.
As of October 31, 2010, the remaining life of the Notes is approximately 4 years.
22
•
in certain situations, when the trading price of the Notes is less than 98 percent of the product of the sale price of the Company’s
common stock and the conversion rate;
•
upon the occurrence of specified corporate transactions described under the Indenture, such as a consolidation, merger or binding share
exchange; or
•
at any time on or after October 15, 2014.
As of
October 31,
2010
Equity component (1)
$
125,530
Liability component:
Principal
$
575,000
Less: debt discount, net (2)
$
(108,153
)
Net carrying amount
$
466,847
(1)
Included in the condensed consolidated balance sheets within additional paid
-
in capital, net of the $1.8 million in equity issuance costs.
(2)
Included in the condensed consolidated balance sheets within 0.75% convertible senior notes and is
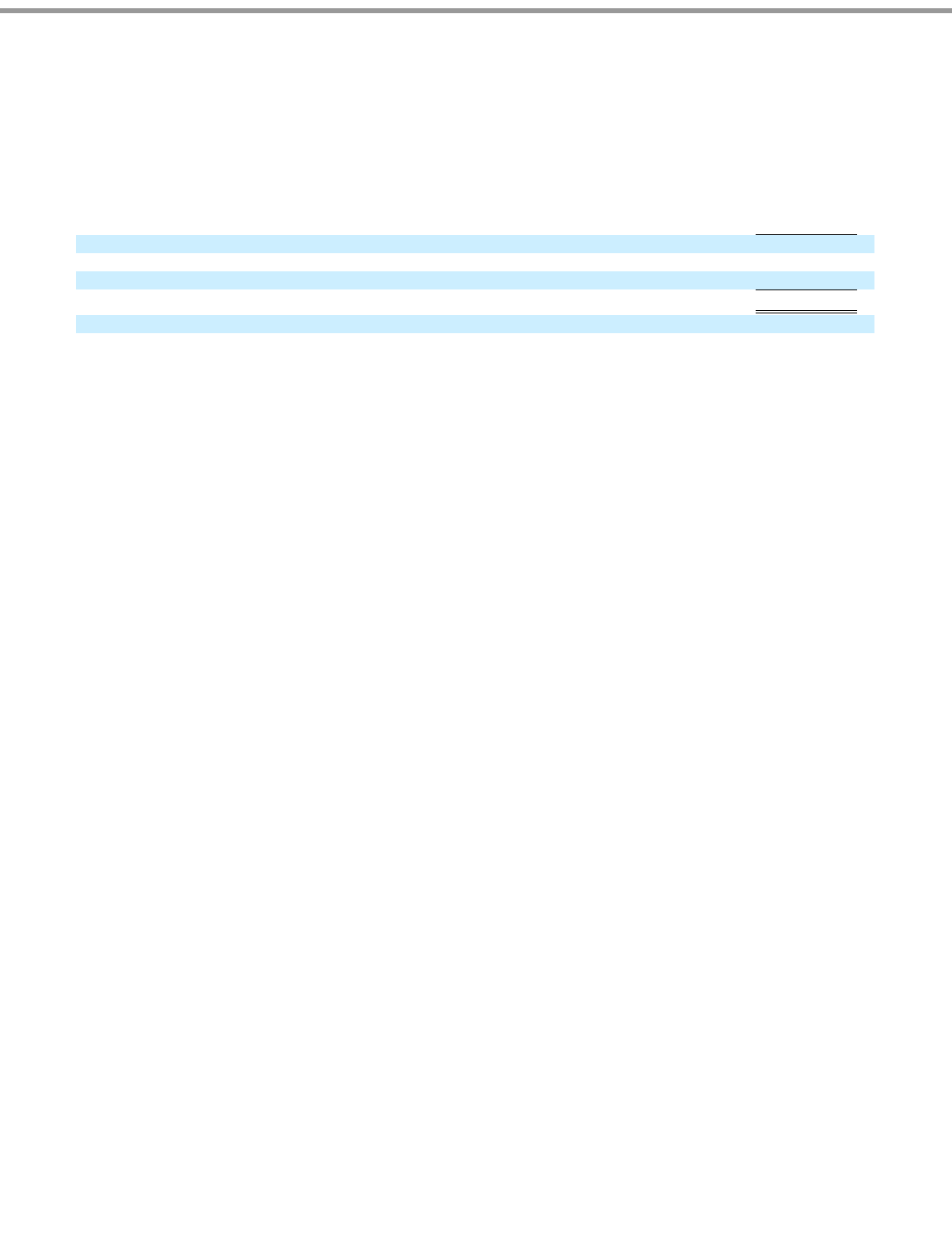
Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
The following table sets forth total interest expense recognized related to the Notes (in thousands):
Note Hedges
To minimize the impact of potential economic dilution upon conversion of the Notes, the Company entered into convertible note hedge
transactions with respect to its common stock (the “Note Hedges”). The Company paid an aggregate amount of $126.5 million for the Note
Hedges. The Note Hedges cover approximately 6.7 million shares of the Company’s common stock at a strike price that corresponds to the
initial conversion price of the Notes, also subject to adjustment, and are exercisable upon conversion of the Notes. The Note Hedges will expire
upon the maturity of the Notes. The Note Hedges are intended to reduce the potential economic dilution upon conversion of the Notes in the
event that the market value per share of the Company’s common stock, as measured under the Notes, at the time of exercise is greater than the
conversion price of the Notes. The Note Hedges are separate transactions and are not part of the terms of the Notes. Holders of the Notes will not
have any rights with respect to the Note Hedges. The Company in January 2010 recorded a deferred tax asset of $51.4 million in connection with
these Note Hedges.
Warrants
Separately, the Company in January 2010 also entered into warrant transactions (the “Warrants”), whereby the Company sold warrants to
acquire, subject to anti-dilution adjustments, up to 6.7 million shares of the Company’s common stock at a strike price of $119.51 per share. The
Company received aggregate proceeds of $59.2 million from the sale of the Warrants. If the market value per share of the Company’s common
stock, as measured under the Warrants, exceeds the strike price of the Warrants, the Warrants will have a dilutive effect on the Company’s
earnings per share. The Warrants are separate transactions, entered into by the Company and are not part of the terms of the Notes or Note
Hedges. Holders of the Notes and Note Hedges will not have any rights with respect to the Warrants.
3. Stockholders’ Equity
Stock Options Issued to Employees
The 1999 Stock Option Plan (the “1999 Plan”) provides for the issuance of incentive and non-statutory options to employees and
nonemployees of the Company. On April 30, 2009, the 1999 Plan expired. The expiration of the 1999 Plan did not affect awards outstanding,
which continue to be governed by the terms and conditions of the 1999 Plan. In addition to the 1999 Plan, the Company maintains the 2004
Equity Incentive Plan, 2004 Employee Stock Purchase Plan and the 2004 Outside Directors Stock Plan. These plans, other than the 2004 Outside
Directors Stock Plan, provide for annual automatic increases on February 1 to the shares reserved for issuance based on the lesser of (i) a specific
percentage of the total number of shares outstanding at year end; (ii) a fixed number of shares; or (iii) a lesser number of shares set by the
Company’s Board of Directors, all as specified in the respective plans.
23
Nine months ended
October 31, 2010
Contractual interest expense
$
3,234
Amortization of debt issuance costs
990
Amortization of debt discount
16,649
$
20,873
Effective interest rate of the liability component
5.86
%

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
On February 1, 2010, 3.5 million additional shares were reserved under the 2004 Equity Incentive Plan pursuant to the automatic increase.
The 2004 Employee Stock Purchase Plan will not be implemented unless and until the Company’s Board of Directors authorizes the
commencement of one or more offerings under the plan. No offering periods have been authorized to date.
In April 2006, the Company’s Board of Directors approved the 2006 Inducement Equity Incentive Plan (the “Inducement Plan”) that
allows for stock option and other equity incentive grants to employees in connection with merger or acquisition activity. In fiscal 2010, the
Board of Directors amended the Inducement Plan to increase the share reserve by 300,000 shares to 700,000 shares total. As of October 31,
2010, there were 303,543 shares of common stock available for grant under the Inducement Plan.
Prior to February 1, 2006, options issued under the Company’
s stock option plans generally had a term of 10 years. After February 1, 2006,
options issued to employees have a term of 5 years.
Stock activity for the nine months ended October 31, 2010 is as follows:
The total intrinsic value of the options exercised during the nine months ended October 31, 2010 and 2009 were $222.9 million and $36.1
million, respectively. The intrinsic value is the difference between the current market value of the stock and the exercise price of the stock
option.
The weighted-average remaining contractual life of vested and expected to vest options is approximately 3.2 years.
As of October 31, 2010, options to purchase 4,122,901 shares were vested at a weighted average exercise price of $32.22 per share and a
remaining weighted-average remaining contractual life of approximately 2.7 years. The total intrinsic value of these vested options as of
October 31, 2010 was $345.7 million.
24
Shares
Available
for Grant
Options Outstanding
Outstanding
Stock
Options
Weighted
-
Average
Exercise Price
Aggregate
Intrinsic Value
(in thousands)
Balance as of January 31, 2010
4,607,929
14,036,371
$
40.36
Increase in options authorized:
2004 Equity Incentive Plan
3,500,000
—
—
Options granted under all plans
(724,675
)
724,675
83.53
Restricted stock unit activity
(93,190
)
—
—
Stock grants to board members for board services and advisory
board members
(37,650
)
—
—
Exercised
—
(
3,631,390
)
31.94
1999 Plan shares expired
(89,804
)
—
—
Cancelled
687,605
(687,605
)
49.00
Balance as of October 31, 2010
7,850,215
10,442,051
$
45.71
$
734,664
Vested or expected to vest
10,117,020
$
45.36
$
715,411
Exercisable at October 31, 2010
4,122,901
$
32.22
$
345,720

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
The following table summarizes information about stock options outstanding as of October 31, 2010:
Restricted stock unit activity for the nine months ended October 31, 2010 is as follows:
The restricted stock units, which upon vesting entitles the holder to one share of common stock for each restricted stock unit, have an
exercise price of $0.001 per share, which is equal to the par value of the Company’s common stock, and vest over 4 years.
The weighted-average fair value of the restricted stock issued for the nine months ended October 31, 2010 and 2009 was $87.37 and
$38.59 per share, respectively.
The Company realized tax benefits of $73.9 million from the exercise, sale or vesting of stock awards during the nine months ended
October 31, 2010.
25
Options Outstanding
Options Vested
Range of Exercise
Prices
Number
Outstanding
Weighted
-
Average
Remaining
Contractual Life
(Years)
Weighted
-
Average
Exercise
Price
Number of
Shares
Weighted
-
Average
Exercise
Price
$0.75 to $25.19
1,127,057
3.5
$
10.37
1,127,057
$
10.37
$25.97
2,336,058
3.1
$
25.97
800,597
$
25.97
$27.20 to $52.28
1,904,794
2.2
$
41.08
1,384,466
$
40.06
$52.30 to $60.96
1,508,149
2.5
$
53.49
679,972
$
53.20
$61.34 to $65.41
105,543
2.9
$
63.34
36,952
$
62.85
$65.44
2,561,644
4.1
$
65.44
—
—
$65.68 to $114.77
898,806
4.1
$
79.83
93,857
$
67.98
10,442,051
3.2
$
45.71
4,122,901
$
32.22
Restricted Stock Units Outstanding
Outstanding
Weighted
-
Average
Exercise Price
Aggregate
Intrinsic
Value
(in thousands)
Balance as of January 31, 2010
2,316,452
$
0.001
Granted
294,324
$
0.001
Cancelled
(201,134
)
$
0.001
Vested and converted to shares
(554,908
)
$
0.001
Balance as of October 31, 2010
1,854,734
$
0.001
$
215,279
Expected to vest
1,739,517
$
201,906

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Common Stock
The following shares of common stock are available for future issuance at October 31, 2010:
4. Acquisitions
On May 7, 2010 the Company acquired for cash the stock of Jigsaw Data Corporation (“Jigsaw”), a provider of crowd-sourced data
services in the cloud. The Company acquired Jigsaw to combine the Company’s CRM applications and enterprise cloud platform with Jigsaw’s
cloud-based model for the automation of acquiring, completing and cleansing business contact data. The Company has included the financial
results of Jigsaw in the condensed consolidated financial statements from the date of acquisition. The total cash consideration for Jigsaw was
approximately $148.5 million. In addition, the Company will potentially make additional payments (“contingent consideration”) totaling up to
$14.4 million in cash, based on the achievement of certain billings targets related to Jigsaw’s services for the one-year period from May 8, 2010
through May 7, 2011. The estimated fair value of the contingent consideration at May 7, 2010 was $13.4 million and is included in the total
purchase price. The Company has recorded and will record the fair value of the contingent consideration each reporting period based on Jigsaw’
s
achievement of meeting its billing targets as it relates to the contingent consideration. The Company’s estimated fair value of the contingent
consideration at October 31, 2010 was $13.9 million. The change in fair value of contingent consideration is recorded in general and
administrative expenses.
The total preliminary purchase price and the fair value of the contingent consideration was allocated to the net tangible and intangible
assets based upon their fair values as of May 7, 2010 as set forth below. The excess of the preliminary purchase price over the net tangible and
intangible assets was recorded as goodwill. The following table summarizes the estimated fair values of the assets and liabilities assumed at the
acquisition date. The primary areas of the preliminary purchase price allocation that are not yet finalized relate to both current and non-current
deferred tax liabilities which are subject to change, pending the finalization of certain tax returns.
26
Options outstanding
10,442,051
Restricted stock units outstanding
1,854,734
Stock available for future grant:
2004 Equity Incentive Plan
6,923,672
2006 Inducement Equity Incentive Plan
303,543
2004 Employee Stock Purchase Plan
1,000,000
2004 Outside Directors Stock Plan
623,000
0.75% Convertible senior notes
6,735,953
Warrants
6,735,953
34,618,906
(in thousands)
Net tangible assets
$
4,347
Intangible assets
28,140
Deferred tax liability
(3,864
)
Goodwill
133,254
Total purchase price
$
161,877

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
The following table sets forth the components of intangible assets acquired in connection with the Jigsaw acquisition:
Customer relationships represent the fair values of the underlying relationships and agreements with Jigsaw’s customers. Developed
service technology and database represents the fair values of the Jigsaw technology and database that contains the business contact data. Trade
name and trademark represents the fair values of brand and name recognition associated with the marketing of Jigsaw’s services. The goodwill
balance is not deductible for tax purposes. The acquisition costs related to Jigsaw were not material.
During the nine months ended October 31, 2010, the Company acquired two privately-held companies for approximately $13.8 million in
cash to expand its products and services. These acquisitions were not significant. The Company has included the financial results of these
companies in its condensed consolidated results from their acquisition dates. The preliminary purchase price allocations for these acquisitions
were based upon the fair values as of the acquisition dates.
5. Joint Venture
During the three months ended October 31, 2010, the Company increased its ownership interest in Salesforce Japan from 73 percent to 96
percent through the purchase of shares held by SunBridge Corporation, a Japanese corporation (“SunBridge”) and certain other shareholders for
cash payments totaling $151.0 million. Salesforce Japan was formed in 2000 as a joint venture between the Company and SunBridge. As a result
of the purchase of the shares held by SunBridge, the joint venture agreement terminated according to its terms. The purchase transaction,
including transaction-related fees totaling $1.1 million, were accounted for as a reduction to Additional paid-in capital and noncontrolling
interest.
6. Commitments and Contingencies
Letters of Credit
As of October 31, 2010, the Company had a total of $11.7 million in letters of credit outstanding for office space in San Francisco,
California, New York City, Singapore, Sweden, United Kingdom, Australia and Switzerland. These letters of credit renew annually and mature
at various dates through September 2021.
27
(in thousands)
Fair value
Useful Life
Developed service technology and database
$
23,560
3 years
Customer relationships
2,440
5 years
Trade name and trademark
2,140
3 years
Total intangible assets subject to amortization
$
28,140

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
Leases
The Company leases office space and equipment under noncancelable operating and capital leases with various expiration dates.
As of October 31, 2010, the future minimum lease payments under noncancelable operating and capital leases are as follows (in
thousands):
The Company’s agreements for the facilities and certain services provide the Company with the option to renew. The Company’s future
contractual obligations would change if it were to exercise these options.
7. Legal Proceedings and Claims
The Company is involved in various legal proceedings arising from the normal course of business activities. In management’s opinion,
resolution of these matters is not expected to have a material adverse impact on the Company’s consolidated results of operations, cash flows or
its financial position. However, depending on the nature and timing of any such dispute, an unfavorable resolution of a matter could materially
affect the Company’s future results of operations, cash flows or financial position.
On May 18, 2010, Microsoft Corporation filed a complaint against the Company in the United States District Court for the Western
District of Washington alleging infringement of nine patents which Microsoft claimed were related to certain aspects of the Company’s products
and services. The complaint sought, among other things, damages, attorneys’ fees and costs, and injunctive relief. On June 24, 2010, the
Company filed a complaint against Microsoft in the United States District Court for the District of Delaware alleging infringement of five of the
Company’s patents related to certain aspects of Microsoft’s products and services. The complaint sought, among other things, damages,
attorneys’ fees and costs, and injunctive relief. On August 2, 2010, the Company entered into a patent cross-license and settlement agreement
with Microsoft and the companies subsequently dismissed their respective cases.
Many of the Company’s subscription agreements require the Company to indemnify its customers for third-party intellectual property
infringement claims, which could increase the cost to the Company of an adverse ruling on such a claim. Any adverse determination related to
intellectual property claims or litigation could prevent the Company from offering its service to others, could be material to its net income or
cash flows (or both) of a particular quarter or could otherwise adversely affect the Company’s operating results.
28
Capital
Leases
Operating
Leases
Fiscal Period:
Remaining three months in fiscal 2011
$
2,540
$
27,340
Fiscal 2012
12,311
98,722
Fiscal 2013
5,713
88,946
Fiscal 2014
2,222
64,679
Fiscal 2015
—
37,908
Thereafter
—
147,343
Total minimum lease payments
22,786
$
464,938
Less: amount representing interest
(1,258
)
Present value of capital lease obligations
$
21,528

Table of Contents
salesforce.com, inc.
Notes to Condensed Consolidated Financial Statements—(Continued)
8. Related-Party Transactions
In January 1999, the salesforce.com/foundation, also referred to as the Foundation, a non-profit public charity, was chartered to build
philanthropic programs that are focused on youth and technology. The Company’s chairman is the chairman of the Foundation. The Company’s
chairman, one of the Company’s employees and one of the Company’s board members hold three of the Foundation’s seven board seats. The
Company is not the primary beneficiary of the Foundation’s activities, and accordingly, the Company does not consolidate the Foundation’s
statement of activities with its financial results.
Since the Foundation’s inception, the Company has provided at no charge certain resources to Foundation employees such as office space.
The value of these items totals approximately $35,000 per quarter.
In addition to the resource sharing with the Foundation, the Company issued the Foundation warrants in August 2002 to purchase 500,000
shares of common stock which were all exercised in prior years. As of October 31, 2010, the Foundation held 124,500 shares of salesforce.com
common stock. Additionally, the Company has donated subscriptions to the Company’s service to other qualified non-profit organizations and
permitted the Foundation to sell such subscriptions to qualified non-profit organizations. The fair value of these donated subscriptions were
approximately $4.0 million per month during the three months ended October 31, 2010. The Company currently plans to continue providing free
subscriptions to qualified non-profit organizations through its relationship with the Foundation.
29

Table of Contents
The following discussion in “Management’s Discussion and Analysis of Financial Condition and Results of Operations” (“MD&A”)
contains forward-looking statements within the meaning of Section 27A of the Securities Act of 1933 and Section 21E of the Securities Exchange
Act of 1934. Forward
-looking statements consist of, among other things, trend analyses, statements regarding future events, future financial
performance, our business strategy and our plan to build our business, our service performance and security, the expenses associated with our
data center capacity, our operating results, our anticipated growth, trends in our business, new application service features, our strategy of
acquiring or making investments in complementary companies, services and technologies, the effect of general economic and market conditions
including sudden declines in the fair value of our investments in cash equivalents and marketable securities, our ability to protect our
intellectual property rights, our ability to develop our brands, the effect of evolving government regulations, the effect of foreign currency
exchange rate and interest rate fluctuations on our financial results, the potential availability of additional tax assets in the future and related
matters, the impact of expensing stock options, the sufficiency of our capital resources, our plan to build our new global headquarters in San
Francisco, and our strategy to be the leading provider of CRM application services and the leading platform on which customers and partners
build enterprise cloud computing applications, of which are based on current expectations, estimates, and forecasts, and the beliefs and
assumptions of our management. Words such as “expects,” “anticipates,” “projects,” “intends,” “plans,” “believes,” “estimates,” variations
of such words, and similar expressions are also intended to identify such forward-looking statements. These forward-looking statements are
subject to risks, uncertainties and assumptions that are difficult to predict. Therefore, actual results may differ materially and adversely from
those expressed in any forward-looking statements. Readers are directed to risks and uncertainties identified below, under “Risk Factors” and
elsewhere in this report, for factors that may cause actual results to be different than those expressed in these forward-looking statements.
Except as required by law, we undertake no obligation to revise or update publicly any forward
-looking statements for any reason.
Overview
We are a leading provider of enterprise cloud computing applications. We provide a comprehensive customer and collaboration
relationship management, or CRM, service to businesses of all sizes and industries worldwide and we provide a technology platform for
customers and developers to build and run business applications.
We were founded in February 1999 and began offering our enterprise CRM application service in February 2000.
Our objective is to be the leading provider of CRM application services and to be the leading platform on which our customers and
partners build enterprise cloud computing applications. Key elements of our strategy include:
We believe the factors that will influence our ability to achieve our objectives include our prospective customers’ willingness to migrate to
an enterprise cloud computing application service; the performance and security of our service; our ability to continue to release, and gain
customer acceptance of, new and improved
30
ITEM 2.
MANAGEMENT
’
S DISCUSSION AND ANALYSIS OF FINANCIAL CONDITION AND RESULTS OF OPERATIONS
•
Strengthening our existing CRM applications;
•
Extending into new functional areas within CRM;
•
Aggressively pursuing new customers and expanding our revenue outside the Americas;
•
Deepening relationships with our existing customer base;
•
Continuing to lead the industry transformation to cloud computing; and
•
Encouraging the development of third
-
party applications on our Force.com
“
cloud computing
”
platform.

Table of Contents
features; successful customer adoption and utilization of our service; acceptance of our service in markets where we have few customers; the
emergence of additional competitors in our market and improved product offerings by existing and new competitors; the location of new data
centers; third-party developers’
willingness to develop applications on our platform; our ability to successfully integrate acquired businesses; and
general economic conditions which could affect our customers’ ability and willingness to purchase our application service, delay the customers’
purchasing decision or affect renewal rates.
To address these factors, we will need to, among other things, continue to add substantial numbers of paying subscriptions, upgrade our
customers to fully featured versions such as our Unlimited Edition, provide high quality technical support to our customers and encourage the
development of third-party applications on our Force.com platform. We plan to invest for future growth by expanding our data center capacity.
We also plan to hire additional personnel, particularly in direct sales, other customer-related areas and research and development. As part of our
growth plans we will have continued focus in the area of retaining customers at the time of renewal. We also plan to: expand our domestic and
international selling and marketing activities; add additional distribution channels; increase our research and development activities to upgrade
and extend our service offerings; develop and support new services and technologies; and, add to our infrastructure to support our growth. We
also regularly evaluate acquisitions or investment opportunities in complementary businesses, joint ventures, services and technologies in an
effort to strengthen and extend our service CRM offerings. We expect to continue to make such investments and acquisitions in the future.
In May 2010, we acquired Jigsaw Data Corporation for a total purchase price consideration of $161.9 million. Jigsaw offers a cloud-based
model for the automation of acquiring, completing and cleansing business contact data. We acquired Jigsaw for its developed technology and
database in order to combine our CRM application with Jigsaw’s crowd-source, data service.
During the three months ended October 31, 2010, we increased our ownership interest in Salesforce Japan from 73 to 96 percent through
the purchase of shares held by SunBridge and certain other stockholders for cash payments totaling $151.0 million. Salesforce Japan was formed
as a joint venture between the Company and SunBridge. As a result of the purchase of the shares held by SunBridge, the joint venture agreement
terminated according to its terms. We intend to acquire the remaining outstanding shares of Salesforce Japan.
We expect marketing and sales costs, which were 47 percent of our total revenues for the nine months ended October 31, 2010 and 46
percent for the same period a year ago, to continue to represent a substantial portion of total revenues in the future as we seek to add and manage
more paying subscribers, and build brand awareness.
On November 1, 2010 we purchased approximately 14 acres of undeveloped land in San Francisco, California, including entitlements and
improvements associated with the land and parking rights in an existing garage for approximately $278.0 million in cash. We have not set a date
for construction yet, but we plan to use the land to build a facility that will become our new global headquarters.
Fiscal Year
Our fiscal year ends on January 31. References to fiscal 2011, for example, refer to the fiscal year ended
January 31, 2011.
Sources of Revenues
We derive our revenues from two sources: (1) subscription revenues, which are comprised of subscription fees from customers accessing
our enterprise cloud computing application service, and from customers purchasing additional support beyond the standard support that is
included in the basic subscription fee; and (2) related professional services and other revenues consisting primarily of training fees. Subscription
and
31

Table of Contents
support revenues accounted for approximately 94 percent of our total revenues during the nine months ended October 31, 2010. Subscription
revenues are driven primarily by the number of paying subscribers of our service and the subscription price of our service. We define a
“customer” as a separate and distinct buying entity (e.g., a company, a distinct business unit of a large corporation, a partnership, etc.) that has
entered into a contract to access our enterprise cloud computing service. We define a “subscription” as a unique user account purchased by a
customer for use by its employee or other customer-authorized user, and each such user is what we call a “subscriber”. The number of paying
subscriptions at each of our customers ranges from one to tens of thousands. None of our customers accounted for more than 5 percent of our
revenues during the three and nine months ended October 31, 2010 and 2009 respectively.
Subscription and support revenues are recognized ratably over the contract terms beginning on the commencement dates of each contract.
The typical subscription and support term is 12 to 24 months, although terms range from one to 60 months. Our subscription and support
contracts are noncancelable, though customers typically have the right to terminate their contracts for cause if we materially fail to perform. We
generally invoice our customers in advance, in annual or quarterly installments, and typical payment terms provide that our customers pay us
within 30 days of invoice. Amounts that have been invoiced are recorded in accounts receivable and in deferred revenue, or in revenue
depending on whether the revenue recognition criteria have been met. In general, we collect our billings in advance of the subscription service
period.
Professional services and other revenues consist of fees associated with consulting and implementation services and training. Our
consulting and implementation engagements are typically billed on a time and materials basis. We also offer a number of classes on
implementing, using and administering our service that are billed on a per person, per class basis. Our typical payment terms provide that our
customers pay us within 30 days of invoice.
We generally recognize revenue ratably over the contract term beginning on the commencement date of each contract. In determining
whether professional services can be accounted for separately from subscription and support revenues, we consider a number of factors, which
are described in “Critical Accounting Policies and Estimates—Revenue Recognition”
below. As we introduce new service offerings, we may not
be able to establish objective and reliable evidence of fair value for these elements of our sales arrangements. As a result, when the professional
services are sold together with subscription services that do not have objective and reliable evidence of fair value, the professional services fees
cannot be accounted for separately, and the entire arrangement is accounted for as a single unit of accounting. In such situations, we recognize
the entire arrangement fee ratably over the term of the subscription contract. Approximately 8 percent and 6 percent of our total deferred revenue
as of October 31, 2010 and January 31, 2010, respectively, related to deferred professional service revenues.
Seasonal Nature of Deferred Revenue and Accounts Receivable
Deferred revenue primarily consists of billings to customers for our subscription service. Over 90 percent of the value of our billings to
customers is for our subscription and support service. We generally invoice our customers in either quarterly or annual cycles, with a
disproportionate weighting towards annual billings in the fourth quarter, primarily as a result of large enterprise account buying patterns.
Additionally, our fourth quarter has historically been our strongest quarter for new business. The year on year compounding effect of this
seasonality in both billing patterns and overall new business is causing the value of invoices that we generate in the fourth quarter for both new
and existing customers to increase as a proportion of our total annual billings.
Accordingly, the sequential quarterly changes in accounts receivable and the related deferred revenue during the first three quarters of our
fiscal year are not necessarily indicative of the billing activity that occurs in the fourth quarter.
32

Table of Contents
The following table sets forth our accounts receivable and deferred revenue balances as of the end of each fiscal quarter:
Cost of Revenues and Operating Expenses
Cost of Revenues. Cost of subscription and support revenues primarily consists of expenses related to hosting our service and providing
support, the costs of data center capacity, depreciation or operating lease expense associated with computer equipment, costs associated with
website development activities, allocated overhead and amortization expense associated with capitalized software related to our application
service and acquired technology. We allocate overhead such as rent and occupancy charges based on headcount. Employee benefit costs and
taxes are allocated based upon a percentage of total compensation expense. As such, general overhead expenses are reflected in each cost of
revenue and operating expense category. Cost of professional services and other revenues consists primarily of employee-
related costs associated
with these services, including stock-based expenses, the cost of subcontractors and allocated overhead. The cost of providing professional
services is significantly higher as a percentage of revenue than for our enterprise cloud computing subscription service due to the direct labor
costs.
We intend to continue to invest additional resources in our enterprise cloud computing application service. For example, we plan to open
additional data centers in the future. Additionally, as we acquire new businesses and technologies, the amortization expense associated with this
activity will be included in cost of revenues. The timing of these additional expenses will affect our cost of revenues, both in terms of absolute
dollars and as a percentage of revenues, in a particular quarterly period.
Research and Development. Research and development expenses consist primarily of salaries and related expenses, including stock-based
expenses, the costs of our development and test data center and allocated overhead. We continue to focus our research and development efforts
on adding new features and services, increasing the functionality and enhancing the ease of use of our enterprise cloud computing application
service. Our proprietary, scalable and secure multi-tenant architecture enables us to provide all of our customers with a service based on a single
version of our application. As a result, we do not have to maintain multiple versions, which enables us to have relatively lower research and
development expenses as compared to traditional enterprise software companies. We expect that in the future, research and development
expenses will increase in absolute dollars as we upgrade and extend our service offerings, develop new technologies and integrate acquired
businesses and technologies.
Marketing and Sales. Marketing and sales expenses are our largest cost and consist primarily of salaries and related expenses, including
stock-based expenses, for our sales and marketing staff, including commissions, payments to partners, marketing programs and allocated
overhead. Marketing programs consist of advertising, events, corporate communications and brand building and product marketing activities.
33
(in thousands)
April 30,
2010
July 31,
2010
October 31,
2010
Fiscal 2011
Accounts receivable, net
$
183,612
$
228,550
$
258,764
Deferred revenue, current and noncurrent
664,529
683,019
694,557
April 30,
2009
July 31,
2009
October 31,
2009
January 31,
2010
Fiscal 2010
Accounts receivable, net
$
145,869
$
168,842
$
191,297
$
320,956
Deferred revenue, current and noncurrent
549,373
549,010
545,435
704,348
April 30,
2008
July 31,
2008
October 31,
2008
January 31,
2009
Fiscal 2009
Accounts receivable, net
$
143,909
$
146,982
$
157,680
$
266,555
Deferred revenue, current and noncurrent
470,297
479,546
469,534
594,026

Table of Contents
We plan to continue to invest in marketing and sales by expanding our domestic and international selling and marketing activities, building
brand awareness and sponsoring additional marketing events. We expect that in the future, marketing and sales expenses will increase in
absolute dollars and continue to be our largest cost.
General and Administrative. General and administrative expenses consist of salaries and related expenses, including stock-based expenses,
for finance and accounting, human resources and management information systems personnel, legal costs, professional fees, other corporate
expenses and allocated overhead. We expect that in the future, general and administrative expenses will increase in absolute dollars as we invest
in our infrastructure and we incur additional employee related costs, professional fees and insurance costs related to the growth of our business
and international expansion. We expect general and administrative costs as a percentage of total revenues to remain flat for the next several
quarters.
Stock-Based Expenses. Our cost of revenues and operating expenses include stock-based expenses related to option and stock awards to
employees and non-employee directors. We recognize our share-based payments as an expense in the statement of operations based on their fair
values and vesting periods. If our stock price increases in the future, stock-based expenses will rise. These charges have been significant in the
past and we expect that they will increase as we hire more employees and seek to retain existing employees.
Joint Venture
In December 2000, we established a Japanese joint venture, Kabushiki Kaisha salesforce.com (“Salesforce Japan”),
with SunBridge, Inc., a
Japanese corporation, to assist us with our sales efforts in Japan. During the three months ended October 31, 2010, we acquired SunBridge’s and
other shareholders’ interest and increased our ownership from 73 to 96 percent of Salesforce Japan. Because of this majority interest, we
consolidate Salesforce Japan’s financial results, which are reflected in each revenue, cost of revenues and expense category in our consolidated
statement of operations. We then record a noncontrolling interest, which reflects the noncontrolling investors’ interest in Salesforce Japan’s
results. We intend to acquire the remaining outstanding shares of Salesforce Japan.
Critical Accounting Policies and Estimates
Our consolidated financial statements are prepared in accordance with accounting principles generally accepted in the United States. The
preparation of these consolidated financial statements requires us to make estimates and assumptions that affect the reported amounts of assets,
liabilities, revenues, costs and expenses, and related disclosures. On an ongoing basis, we evaluate our estimates and assumptions. Our actual
results may differ from these estimates under different assumptions or conditions.
We believe that of our significant accounting policies, which are described in note 1 to our condensed consolidated financial statements,
the following accounting policies involve a greater degree of judgment and complexity. Accordingly, these are the policies we believe are the
most critical to aid in fully understanding and evaluating our condensed consolidated financial condition and results of operations.
Revenue Recognition. We recognize revenue when all of the following conditions are satisfied: (1) there is persuasive evidence of an
arrangement; (2) the service has been provided to the customer; (3) the collection of our fees is reasonably assured; and (4) the amount of fees to
be paid by the customer is fixed or determinable. Our arrangements do not contain general rights of return.
We recognize subscription revenues ratably over the contract terms beginning on the commencement dates of each contract. Support
revenues from customers who purchase our premium support offerings are recognized similarly over the term of the support contract. As part of
their subscription agreements, customers generally benefit from new features and functionality with each release at no additional cost. In
situations where we have contractually committed to an individual customer specific technology, we defer all of the revenue for that customer
until the technology is delivered and accepted. Once delivery occurs, we then recognize the revenue over the remaining contract term.
34

Table of Contents
Consulting services and training revenues are accounted for separately from subscription and support revenues when these services have
value to the customer on a standalone basis and there is objective and reliable evidence of fair value of each deliverable. When accounted for
separately, revenues are recognized as the services are rendered for time and material contracts, and when the milestones are achieved and
accepted by the customer for fixed price contracts. The majority of our consulting service contracts are on a time and material basis. Training
revenues are recognized after the services are performed. For revenue arrangements with multiple deliverables, such as an arrangement that
includes subscription, premium support, consulting or training services, we allocate the total amount the customer will pay to the separate units
of accounting based on their relative fair values, as determined by the price of the undelivered items when sold separately.
In determining whether the consulting services can be accounted for separately from subscription and support revenues, we consider the
following factors for each consulting agreement: availability of the consulting services from other vendors, whether objective and reliable
evidence for fair value exists for the undelivered elements, the nature of the consulting services, the timing of when the consulting contract was
signed in comparison to the subscription service start date, and the contractual dependence of the subscription service on the customer’s
satisfaction with the consulting work. If a consulting arrangement does not qualify for separate accounting, we recognize the consulting revenue
ratably over the remaining term of the subscription contract. Additionally, in these situations we defer the direct costs of the consulting
arrangement and amortize those costs over the same time period as the consulting revenue is recognized. The deferred cost on our condensed
consolidated balance sheet totaled $27.8 million at October 31, 2010 and $19.1 million at January 31, 2010. Such amounts are included in
prepaid expenses and other current assets and other assets, net.
Accounting for Deferred Commissions. We defer commission payments to our direct sales force. The commissions are deferred and
amortized to sales expense over the non-cancelable terms of the related subscription contracts with our customers, which are typically 12 to 24
months. The commission payments, which are paid in full the month after the customer’s service commences, are a direct and incremental cost
of the revenue arrangements. The deferred commission amounts are recoverable through the future revenue streams under the non-cancelable
customer contracts. We believe this is the preferable method of accounting as the commission charges are so closely related to the revenue from
the non-cancelable customer contracts that they should be recorded as an asset and charged to expense over the same period that the subscription
revenue is recognized.
During the nine months ended October 31, 2010, we deferred $65.2 million of commission expenditures and we amortized $57.6 million to
sales expense. During the same period a year ago, we deferred $43.0 million of commission expenditures and we amortized $46.0 million to
sales expense. Deferred commissions on our condensed consolidated balance sheet totaled $83.2 million at October 31, 2010 and $75.5 million
at January 31, 2010.
Accounting for Stock-Based Awards. We recognize the fair value of our stock awards on a straight-line basis over the requisite service
period of the award, which is the vesting term of four years.
We recognized stock-based expense of $78.7 million, or 7 percent of revenue, during the nine months ended October 31, 2010. The
requirement to expense stock-based awards will continue to materially reduce our reported results of operations. As of October 31, 2010, we had
an aggregate of $237.7 million of stock compensation remaining to be amortized to expense over the remaining requisite service period of the
underlying awards. We currently expect this stock compensation balance to be amortized as follows: $29.3 million during the remaining three
months of fiscal 2011; $101.4 million during fiscal 2012; $64.7 million during fiscal 2013; $38.2 million during fiscal 2014; and $4.1 million
during fiscal 2015. These amounts reflect only outstanding stock awards as of October 31, 2010 and assume no forfeiture activity. We expect to
continue to issue share-based awards to our employees in future periods.
35

Table of Contents
We recognize as an operating expense the payroll and social tax costs when stock options are exercised. The impact of stock-
based expense
in the future is dependent upon, among other things, the timing of when we hire additional employees, the effect of long-
term incentive strategies
involving stock awards in order to continue to attract and retain employees, the total number of stock awards granted, the fair value of the stock
awards at the time of grant, changes in estimated forfeiture assumption rates and the tax benefit that we may or may not receive from stock-
based
expenses. Additionally, we are required to use an option-pricing model to determine the fair value of stock option awards. This determination of
fair value is affected by our stock price as well as assumptions regarding a number of highly complex and subjective variables. These variables
include, but are not limited to, our expected stock price volatility over the term of the awards.
As of October 31, 2010, there were 1.9 million restricted stock units outstanding. We plan to continue awarding restricted stock units to
our employees in the future. The restricted stock units, which upon vesting entitles the holder to one share of common stock for each restricted
stock unit, have an exercise price of $0.001 per share, which is equal to the par value of our common stock, and vest over 4 years. The fair value
of the restricted stock units is based on our closing stock price on the date of grant, and compensation expense, net of estimated forfeitures, is
recognized on a straight-line basis over the vesting period.
Accounting for Income Taxes.
We account for income taxes using the liability method, which requires the recognition of deferred tax assets
or liabilities for the tax-effected temporary differences between the financial reporting and tax bases of our assets and liabilities and for net
operating loss and tax credit carryforwards. The tax expense or benefit for unusual items, or certain adjustments to the valuation allowance are
treated as discrete items in the interim period in which the events occur.
Our effective tax rate could be adversely affected by changes in the mix of earnings and losses in countries with differing statutory tax
rates, certain non-deductible expenses as a result of acquisitions, the valuation of deferred tax assets and liabilities, and changes in tax laws and
accounting principles.
36

Table of Contents
Results of Operations
The following tables set forth selected data for each of the periods indicated and are in thousands. All data is unaudited.
37
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Revenues:
Subscription and support
$
402,948
$
306,870
$
1,122,611
$
882,078
Professional services and other
26,139
23,679
77,661
69,456
Total revenues
429,087
330,549
1,200,272
951,534
Cost of revenues:
Subscription and support
54,089
40,745
147,127
116,744
Professional services and other
28,042
24,825
84,375
73,122
Total cost of revenues
82,131
65,570
231,502
189,866
Gross profit
346,956
264,979
968,770
761,668
Operating expenses:
Research and development
47,305
32,763
130,357
95,450
Marketing and sales
200,544
152,166
558,812
436,647
General and administrative
63,951
49,909
181,713
139,818
Total operating expenses
311,800
234,838
870,882
671,915
Income from operations
35,156
30,141
97,888
89,753
Investment income
11,699
7,503
28,309
19,780
Interest expense
(7,374
)
(292
)
(21,619
)
(793
)
Other expense
(921
)
(336
)
(4,659
)
(1,037
)
Income before provision for income taxes and noncontrolling interest
38,560
37,016
99,919
107,703
Provision for income taxes
(16,192
)
(15,573
)
(41,092
)
(45,426
)
Consolidated net income
22,368
21,443
58,827
62,277
Less: net income attributable to noncontrolling interest
(1,296
)
(752
)
(5,266
)
(1,952
)
Net income attributable to salesforce.com
$
21,072
$
20,691
$
53,561
$
60,325
As of
October 31,
2010
January 31,
2010 (1)
October 31,
2009
Balance sheet data:
Cash, cash equivalents and marketable securities
$
1,802,440
$
1,727,048
$
1,070,092
Deferred revenue, current and noncurrent
694,557
704,348
545,435
(1) Cash, cash equivalents and marketable securities includes the net proceeds from our January 2010 convertible senior note offering totaling
approximately $500.0 million as described in Note 2 in the condensed consolidated financial statements.
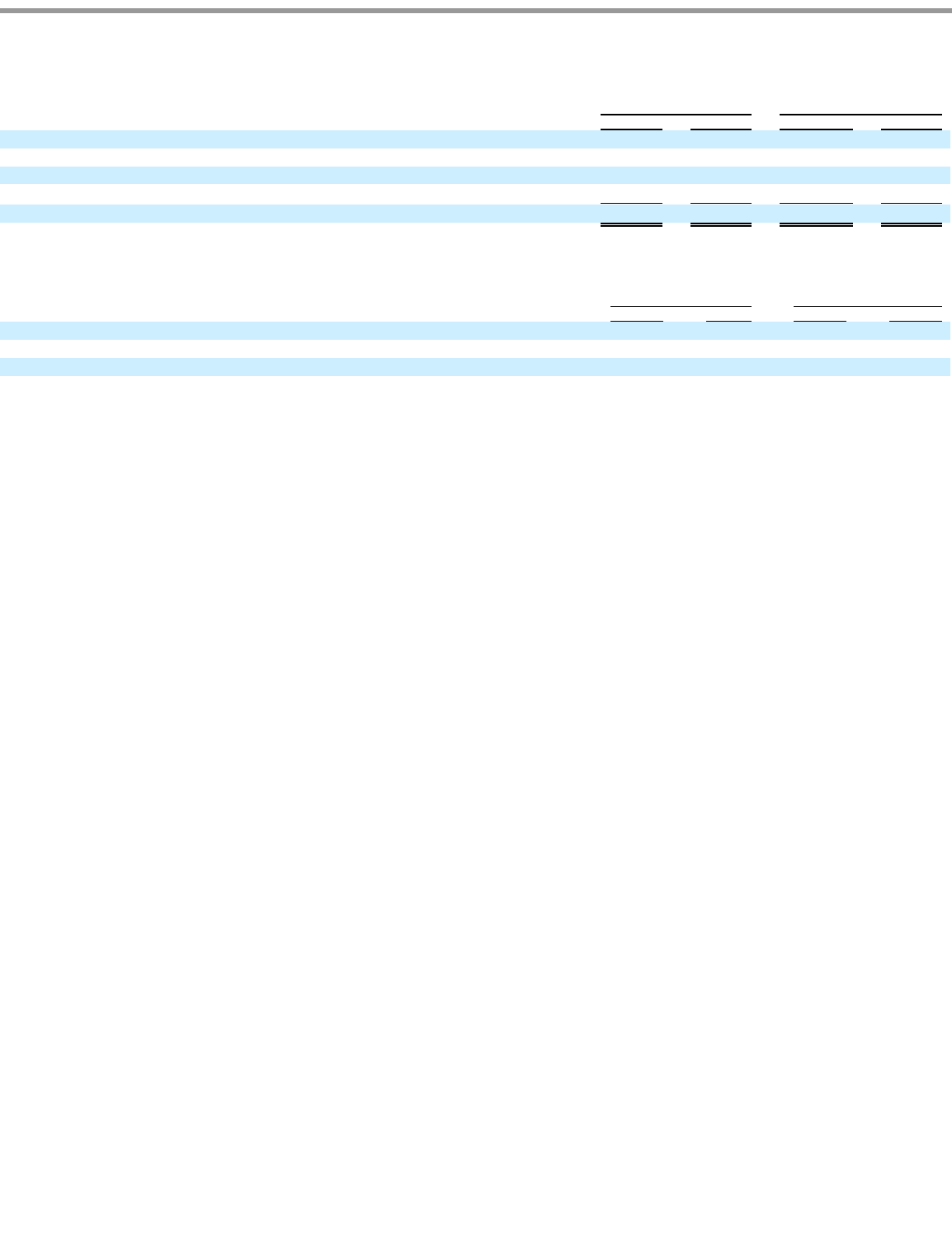
Table of Contents
Cost of revenues and operating expenses include the following amounts related to stock-based awards.
38
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Revenues by geography:
Americas
$
292,540
$
232,802
$
826,493
$
679,460
Europe
76,464
60,761
208,851
168,355
Asia Pacific
60,083
36,986
164,928
103,719
$
429,087
$
330,549
$
1,200,272
$
951,534
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Cost of revenues
$
2,357
$
2,995
$
8,617
$
9,322
Research and development
3,976
2,707
12,119
8,741
Marketing and sales
11,969
9,055
36,496
28,314
General and administrative
7,330
5,650
21,483
16,570

Table of Contents
The following tables set forth selected consolidated statements of operations data for each of the periods indicated as a percentage of total
revenues.
39
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Revenues:
Subscription and support
94
%
93
%
94
%
93
%
Professional services and other
6
7
6
7
Total revenues
100
100
100
100
Cost of revenues:
Subscription and support
13
12
12
12
Professional services and other
6
8
7
8
Total cost of revenues
19
20
19
20
Gross profit
81
80
81
80
Operating expenses:
Research and development
11
10
11
10
Marketing and sales
47
46
47
46
General and administrative
15
15
15
15
Total operating expenses
73
71
73
71
Income from operations
8
9
8
9
Investment income
3
2
2
2
Interest expense
(2
)
—
(
2
)
—
Other expense
—
—
—
—
Income before provision for income taxes and noncontrolling interest
9
11
8
11
Provision for income taxes
(4
)
(5
)
(3
)
(5
)
Consolidated net income
5
6
5
6
Less: net income attributable to noncontrolling interest
—
—
(
1
)
—
Net income attributable to salesforce.com
5
%
6
%
4
%
6
%
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Revenues by geography:
Americas
68
%
70
%
69
%
71
%
Europe
18
18
17
18
Asia Pacific
14
12
14
11
100
%
100
%
100
%
100
%
Three months ended
October 31,
Nine months ended
October 31,
2010
2009
2010
2009
Stock
-
based expenses:
Cost of revenues
—
%
1
%
1
%
1
%
Research and development
1
1
1
1
Marketing and sales
3
3
3
3
General and administrative
2
1
2
2

Table of Contents
Three Months Ended October 31, 2010 and 2009
Revenues.
Total revenues were $429.1 million for the three months ended October 31, 2010, compared to $330.5 million during the same period a
year ago, an increase of $98.5 million, or 30 percent. Subscription and support revenues were $403.0 million, or 94 percent of total revenues, for
the three months ended October 31, 2010, compared to $306.9 million, or 93 percent of total revenues, during the same period a year ago. The
increase in subscription and support revenues was due primarily to new customers, upgrades and additional subscriptions from existing
customers and improvement in renewal rates over the past twelve months. Professional services and other revenues were $26.1 million, or 6
percent of total revenues, for the three months ended October 31, 2010, compared to $23.7 million, or 7 percent of total revenues, for the same
period a year ago. The increase in professional services and other revenues was primarily due to the higher demand for services from an
increased number of customers.
Revenues in Europe and Asia Pacific accounted for $136.5 million, or 32 percent of total revenues, for the three months ended October 31,
2010, compared to $97.7 million, or 30 percent of total revenues, during the same period a year ago, an increase of $38.8 million, or 40 percent.
The increase in revenues outside of the Americas was the result of our efforts to expand internationally. Additionally, the value of the U.S. dollar
relative to foreign currencies contributed to a slight decrease in revenues outside the Americas for the three months ended October 31, 2010 as
compared to the same period a year ago. The foreign currency impact had the effect of reducing our aggregate revenues by $3.7 million
compared to the same period a year ago. As part of our overall growth, we expect the percentage of our revenues generated in Europe and Asia
Pacific to continue to increase as a percentage of our total revenues.
Cost of Revenues .
Cost of revenues was $82.1 million, or 19 percent of total revenues, for three months ended October 31, 2010, compared to $65.6 million,
or 20 percent of total revenues, for the same period a year ago, an increase of $16.6 million. The increase in absolute dollars was primarily due to
an increase of $4.8 million in employee-related costs, an increase of $2.2 million in service delivery costs, primarily due to our efforts in
increasing data center capacity, an increase of $5.0 million in depreciation and amortization expenses including amortization expense related to
our acquisition of Jigsaw and other acquisition activity, an increase of $3.3 million in outside subcontractor and other service costs and an
increase of $1.6 million in allocated overhead. These increases were offset by a decrease of $0.6 million in stock-
based expenses. The cost of the
additional professional services headcount resulted in the cost of professional services and other revenues to be in excess of the related revenue
for the three months ended
40
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Percent
Subscription and support
$
402,948
$
306,870
$
96,078
31
%
Professional services and other
26,139
23,679
2,460
10
%
Total revenues
$
429,087
$
330,549
$
98,538
30
%
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Subscription and support
$
54,089
$
40,745
$
13,344
Professional services and other
28,042
24,825
3,217
Total cost of revenues
$
82,131
$
65,570
$
16,561
Percent of total revenues
19
%
20
%

Table of Contents
October 31, 2010 by $1.9 million. This reduction was the result of reduced utilization of existing professional services staff caused by lowered
customer demand. We expect the cost of professional services and other revenue to continue to be in excess of the related revenue during fiscal
2011. We plan to continue to make this investment since our professional services are primarily designed to accelerate the adoption and
expanded use by our customers of our enterprise cloud computing application service.
Research and Development .
Research and development expenses were $47.3 million, or 11 percent of total revenues, during the three months ended October 31, 2010,
compared to $32.8 million, or 10 percent of total revenues, during the same period a year ago, an increase of $14.5 million. The increase in
absolute dollars was due to an increase of $10.8 million in employee-related costs, an increase of $1.3 million in stock-based expenses, and an
increase of $2.1 million in allocated overhead. We increased our research and development headcount by 34 percent since October 31, 2009 in
order to upgrade and extend our service offerings and develop new technologies.
Marketing and Sales .
Marketing and sales expenses were $200.5 million, or 47 percent of total revenues, during the three months ended October 31, 2010,
compared to $152.2 million, or 46 percent of total revenues, during the same period a year ago, an increase of $48.4 million. The increase in
absolute dollars was primarily due to increases of $34.1 million in employee related costs, $2.9 million in stock-based expenses, $0.2 million of
amortized purchased intangibles which includes amortization expense related to our acquisition of Jigsaw and other acquisition activity, an
increase of $6.1 million in advertising costs and marketing and event costs, $0.3 million in outside subcontractor and other service costs and an
increase of $4.8 million in allocated overhead. Our marketing and sales headcount increased by 26 percent since October 31, 2009 as we hired
additional sales personnel to focus on adding new customers and increasing penetration within our existing customer base. Some of the increase
in headcount was due to the acquisition of Jigsaw in May 2010.
General and Administrative.
General and administrative expenses were $64.0 million, or 15 percent of total revenues, during the three months ended October 31, 2010,
compared to $49.9 million, or 15 percent of total revenues, during the same period a year ago, an increase of $14.0 million. The increase was
primarily due to $13.6 million increase in
41
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Research and development
$
47,305
$
32,763
$
14,542
Percent of total revenues
11
%
10
%
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Marketing and sales
$
200,544
$
152,166
$
48,378
Percent of total revenues
47
%
46
%
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
General and administrative
$
63,951
$
49,909
$
14,042
Percent of total revenues
15
%
15
%

Table of Contents
employee-related costs. Our general and administrative headcount increased by 22 percent since October 31, 2009 as we added personnel to
support our growth.
Income from Operations.
Income from operations during the three months ended October 31, 2010 was $35.2 million and included $25.6 million of stock-based
expenses and $5.9 million of amortization of purchased intangibles and acquired developed technology. During the same period a year ago,
operating income was $30.1 million and included $20.4 million of stock-based expenses and $2.8 million of amortization of purchased
intangibles and acquired developed technology.
Investment income.
Investment income consists of income on cash and marketable securities balances. Investment income was $11.7 million for the three
months ended October 31, 2010 and was $7.5 million during the same period a year ago. The increase was primarily due to the increase in cash
equivalents and marketable securities balances resulting from cash generated by operating activities, proceeds from our convertible senior note
offering in January 2010 and the proceeds from stock option exercises.
Interest expense.
Interest expense consists primarily of interest on our convertible senior notes and capital leases. Interest expense was $7.4 million during
the three months ended October 31, 2010 and was $0.3 million during the same period a year ago. The increase was primarily due to interest
expense associated with the January 2010 issuance of $575.0 million of convertible senior notes and capital leases associated with equipment in
expanding our data center capacity.
Other expense.
42
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Income from operations
$
35,156
$
30,141
$
5,015
Percent of total revenues
8
%
9
%
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Investment income
$
11,699
$
7,503
$
4,196
Percent of total revenues
3
%
2
%
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Interest expense
$
(7,374
)
$
(292
)
$
(7,082
)
Percent of total revenues
2
%
0
%
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Other expense
$
(921
)
$
(336
)
$
(585
)

Table of Contents
Other expense primarily consists of foreign currency transaction gains and losses. Other expense increased due to realized and unrealized
losses on foreign currency transactions for the three months ended October 31, 2010 when compared to the same period a year ago.
Provision for Income Taxes.
Our effective tax rate of 42 percent for the three months ended October 31, 2010 was higher than the federal statutory rate of 35 percent
primarily due to state income taxes, foreign tax rate differential, non-deductible expenses as a result of acquisitions and the unfavorable impact
of a change in California tax law, which were partially offset by California tax credits. Similarly, our effective tax rate of 42 percent for the three
months ended October 31, 2009 was higher than the federal statutory rate of 35 percent primarily due to state income taxes, foreign tax rate
differential and the unfavorable impact of a change in California tax law, which were partially offset by federal and California tax credits.
Nine Months Ended October 31, 2010 and 2009
Revenues.
Total revenues were $1,200.3 million for the nine months ended October 31, 2010, compared to $951.5 million during the same period a
year ago, an increase of $248.7 million, or 26 percent. Subscription and support revenues were $1,122.6 million, or 94 percent of total revenues,
for the nine months ended October 31, 2010, compared to $882.1 million, or 93 percent of total revenues, during the same period a year ago. The
increase in subscription and support revenues was due primarily to new customers, upgrades and additional subscriptions from existing
customers and improvement in renewal rates. Professional services and other revenues were $77.7 million, or 6 percent of total revenues, for the
nine months ended October 31, 2010, compared to $69.5 million, or 7 percent of total revenues, for the same period a year ago. The increase in
professional services and other revenues was due primarily to the higher demand for services from an increased number of customers.
Revenues in Europe and Asia Pacific accounted for $373.8 million, or 31 percent of total revenues, for the nine months ended October 31,
2010, compared to $272.1 million, or 29 percent of total revenues, during the same period a year ago, an increase of $101.7 million, or 37
percent. The increase in revenues outside of the Americas was the result of our efforts to expand internationally. Additionally, the value of the
U.S. dollar relative to foreign currencies contributed to the slight decrease in revenues outside the Americas for the nine months ended
October 31, 2010 as compared to the same period a year ago. The foreign currency impact had the effect of reducing our aggregate revenues by
$4.0 million compared to the same period a year ago. As part of our overall growth, we expect the percentage of our revenues generated in
Europe and Asia Pacific to continue to increase as a percentage of our total revenues.
43
Three Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Provision for income taxes
$
(16,192
)
$
(15,573
)
$
(619
)
Effective tax rate
42
%
42
%
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Percent
Subscription and support
$
1,122,611
$
882,078
$
240,533
27
%
Professional services and other
77,661
69,456
8,205
12
%
Total revenues
$
1,200,272
$
951,534
$
248,738
26
%

Table of Contents
Cost of Revenues.
Cost of revenues was $231.5 million, or 19 percent of total revenues, for nine months ended October 31, 2010, compared to $189.9
million, or 20 percent of total revenues, for the same period a year ago, an increase of $41.6 million. The increase in absolute dollars was
primarily due to an increase of $16.1 million in employee-
related costs, an increase of $9.7 million in depreciation and amortization expenses, an
increase of $8.2 million in outside subcontractor and other service costs, an increase of $4.9 million in service delivery costs and an increase of
$2.1 million in allocated overhead. These increases were offset by a decrease of $0.7 million in stock based expenses. The cost of the additional
professional services headcount resulted in the cost of professional services and other revenues to be in excess of the related revenue for the nine
months ended October 31, 2010 by $6.7 million. We increased the professional services headcount in order to meet the current and anticipated
demand for our consulting and training services as our subscriber base has expanded to include more large businesses and as we have expanded
internationally.
Research and Development.
Research and development expenses were $130.4 million, or 11 percent of total revenues, during the nine months ended October 31, 2010,
compared to $95.5 million, or 10 percent of total revenues, during the same period a year ago, an increase of $34.9 million. The increase in
absolute dollars was due to an increase of $26.9 million in employee-related costs, an increase of $3.4 million in stock-based expenses and an
increase of $3.3 million in allocated overhead. We increased our research and development headcount by 34 percent since October 31, 2009 in
order to upgrade and extend our service offerings and develop new technologies. Some of the increase in headcount was due to acquired
businesses.
Marketing and Sales.
Marketing and sales expenses were $558.8 million, or 47 percent of total revenues, during the nine months ended October 31, 2010,
compared to $436.6 million, or 46 percent of total revenues, during the same period a year ago, an increase of $122.2 million. The increase in
absolute dollars was primarily due to increases of $95.7 million in employee related costs, $8.2 million in stock-based expenses, an increase of
$7.6 million in advertising costs and marketing and event costs and an increase of $8.7 in allocated overhead. Our marketing and sales
44
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Subscription and support
$
147,127
$
116,744
$
30,383
Professional services and other
84,375
73,122
11,253
Total cost of revenues
$
231,502
$
189,866
$
41,636
Percent of total revenues
19
%
20
%
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Research and development
$
130,357
$
95,450
$
34,907
Percent of total revenues
11
%
10
%
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Marketing and sales
$
558,812
$
436,647
$
122,165
Percent of total revenues
47
%
46
%

Table of Contents
headcount increased by 26 percent since October 31, 2009 as we hired additional sales personnel to focus on adding new customers and
increasing penetration within our existing customer base. Some of the increase in headcount was due to acquired businesses.
General and Administrative.
General and administrative expenses were $181.7 million, or 15 percent of total revenues, during the nine months ended October 31, 2010,
compared to $139.8 million, or 15 percent of total revenues, during the same period a year ago, an increase of $41.9 million. The increase was
primarily due to an increase in $32.7 million employee-related costs, an increase of $4.9 million in stock-
based expenses, and an increase of $2.6
in depreciation and amortization expenses. Our general and administrative headcount increased by 22 percent since October 31, 2009 as we
added personnel to support our growth.
Income from Operations.
Income from operations during the nine months ended October 31, 2010 was $97.9 million and included $78.7 million of stock-based
expenses and $13.4 million of amortization of purchased intangibles and acquired developed technology. During the same period a year ago,
operating income was $89.8 million and included $62.9 million of stock-based expenses and $8.1 million of amortization of purchased
intangibles.
Investment income.
Investment income consists of income on cash and marketable securities balances. Investment income was $28.3 million for the nine
months ended October 31, 2010 and was $19.8 million during the same period a year ago. The increase was primarily due to increased realized
gains and the increase in marketable securities balances resulting from cash generated by operating activities, proceeds from our senior note
offering in January 2010 and the proceeds from stock option exercises.
Interest expense.
45
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
General and administrative
$
181,713
$
139,818
$
41,895
Percent of total revenues
15
%
15
%
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Income from operations
$
97,888
$
89,753
$
8,135
Percent of total revenues
8
%
9
%
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Investment income
$
28,309
$
19,780
$
8,529
Percent of total revenues
2
%
2
%
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Interest expense
$
(21,619
)
$
(793
)
$
(20,826
)
Percent of total revenues
2
%
0
%

Table of Contents
Interest expense consists primarily of interest on our convertible senior notes and capital leases. Interest expense was $21.6 million during
the nine months ended October 31, 2010 and was $0.8 million during the same period a year ago. The increase was primarily due to interest
expense associated with the January 2010 issuance of $575.0 million of convertible senior notes and capital leases associated with equipment in
expanding our data center capacity.
Other expense.
Other expense primarily consists of foreign currency translation adjustments. Other expense increased due to realized and unrealized losses
on foreign currency translations for the nine months ended October 31, 2010 when compared to the same period a year ago.
Provision for Income Taxes.
Our effective tax rate of 41 percent for the nine months ended October 31, 2010 was higher than the federal statutory rate of 35 percent
primarily due to state income taxes, foreign tax rate differential, non-deductible expenses as a result of acquisitions, and the unfavorable impact
of a change in California tax law, which were partially offset by California tax credits. Similarly, our effective tax rate of 42 percent for the nine
months ended October 31, 2009 was higher than the federal statutory rate of 35 percent primarily due to state income taxes, foreign tax rate
differential, and the unfavorable impact of a change in California tax law, which were partially offset by Federal and California tax credits.
In February 2009, the State of California enacted several income tax law changes which include an election to apply a single-sales factor
apportionment formula and adoption of a market sourcing approach for service income that will impact us beginning in fiscal 2012. As a result,
we re-valued the anticipated future tax effects of California temporary differences including stock-based compensation and purchased
intangibles, starting in the first quarter ended April 30 2009. Accordingly, we recorded a tax expense of $2.5 million during the first nine months
ended October 31, 2009.
New Accounting Pronouncement
In September 2009, the FASB issued Accounting Standards Update No. 2009-13, “ Multiple-Deliverable Revenue Arrangements—a
consensus of the FASB Emerging Issues Task Force ” (ASU 2009-13). It updates the existing multiple-element revenue arrangements guidance
currently included under ASC 605-25, which originated primarily from the guidance in EITF Issue No. 00-21, “ Revenue Arrangements with
Multiple Deliverables
” (EITF 00-21). The revised guidance primarily provides two significant changes: 1) eliminates the need for objective and
reliable evidence of the fair value for the undelivered element in order for a delivered item to be treated as a separate unit of accounting, and 2)
eliminates the residual method to allocate the arrangement consideration. In addition, the guidance also expands the disclosure requirements for
revenue recognition. ASU 2009-13 will be effective for the first annual reporting period beginning on or after June 15, 2010. We believe the
future impact of this new accounting pronouncement will not be material to consolidated net income.
46
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Other expense
$
(4,659
)
$
(1,037
)
$
(3,622
)
Nine Months Ended
October 31,
Variance
(In thousands)
2010
2009
Dollars
Provision for income taxes
$
(41,092
)
$
(45,426
)
$
4,334
Effective tax rate
41
%
42
%

Table of Contents
Liquidity and Capital Resources
At October 31, 2010, our principal sources of liquidity were cash, cash equivalents and marketable securities totaling $1.8 billion and
accounts receivable of $258.8 million.
Net cash provided by operating activities was $293.3 million during the nine months ended October 31, 2010 and $179.4 million during
the same period a year ago. The improvement in cash flow was due primarily to the growth in our customer base and improving renewal rates
and the associated increase in billings and collections. Cash provided by operating activities has historically been affected by: the amount of net
income; sales of subscriptions, support and professional services; changes in working capital accounts, particularly increases and seasonality in
accounts receivable and deferred revenue as described above, and the timing of commission and bonus payments, collections from large
enterprise customers; add-backs of non-cash expense items such as depreciation and amortization, amortization of debt discount and the expense
associated with stock-based awards.
Net cash used in investing activities was $679.8 million during the nine months ended October 31, 2010 and $473.6 million during the
same period a year ago. The net cash used in investing activities during the nine months ended October 31, 2010 primarily related to the
purchase of Jigsaw in May 2010, investment of cash balances and capital expenditures, the deposit on undeveloped land in San Francisco, and
investments in privately-held companies.
Net cash provided by financing activities was $3.4 million during the nine months ended October 31, 2010 and $59.5 million during the
same period a year ago. Net cash provided by financing activities during the nine months ended October 31, 2010 consisted of $116.0 million of
proceeds from the exercise of employee stock options and $46.8 million of excess tax benefits from employee stock plans, both of which were
offset by the $152.2 million in purchases of shares held by others in Salesforce Japan and $7.2 million of principal payments on capital leases.
In January 2010, we issued $575.0 million of 0.75% convertible senior notes due January 15, 2015 (the “Notes”) and concurrently entered
into convertible notes hedges (the “Note Hedges”) and separate warrant transactions (the “Warrants”). The Notes will mature on January 15,
2015, unless earlier converted. As of October 31, 2010, the Notes have not been repurchased or converted. We also have not received any shares
under the Note Hedges or delivered cash or shares under the Warrants. For further information, see Note 2 to the condensed consolidated
financial statements.
On November 1, 2010, we purchased approximately 14 acres of undeveloped land in San Francisco, California, including entitlements and
improvements associated with the land and parking rights in an existing garage for approximately $278.0 million in cash. No date for
construction is set, but we plan to use the land to build our new global headquarters. We plan to devote additional financial resources in the
future to build our new headquarters.
Our cash, cash equivalents and marketable securities are comprised of corporate notes and obligations, U.S. agency obligations, U.S.
treasury securities, mortgage backed securities, collateralized mortgage obligations, time deposits, money market mutual funds, government
obligations and municipal securities.
As of October 31, 2010 we have a total of $11.7 million in letters of credit outstanding in favor of our landlords for office space in San
Francisco, California, New York City, Singapore, Sweden, United Kingdom, Australia and Switzerland. To date, no amounts have been drawn
against the letters of credit, which renew annually and mature at various dates through September 2021.
We do not have any special purpose entities, and other than operating leases for office space and computer equipment, we do not engage in
off-balance sheet financing arrangements. Additionally, we currently do not have a bank line of credit.
47

Table of Contents
Our principal commitments consist of obligations under leases for office space and co-location facilities for data center capacity and the
development and test data center, and computer equipment and furniture and fixtures. At October 31, 2010, the future non-cancelable minimum
payments under these commitments were as follows (in thousands):
Our lease agreements provide us with the option to renew. Our future operating lease obligations would change if we exercised these
options and if we entered into additional operating lease agreements as we expand our operations.
We believe our existing cash, cash equivalents and short-term marketable securities and cash provided by operating activities will be
sufficient to acquire the remaining outstanding shares of our subsidiary, Salesforce Japan, meet our working capital and other capital expenditure
needs over the next 12 months.
48
Capital
Leases
Operating
Leases
Fiscal Period:
Remaining three months in fiscal 2011
$
2,540
$
27,340
Fiscal 2012
12,311
98,722
Fiscal 2013
5,713
88,946
Fiscal 2014
2,222
64,679
Fiscal 2015
—
37,908
Thereafter
—
147,343
Total minimum lease payments
22,786
$
464,938
Less: amount representing interest
(1,258
)
Present value of capital lease obligations
$
21,528

Table of Contents
Foreign currency exchange risk
Our results of operations and cash flows are subject to fluctuations due to changes in foreign currency exchange rates, particularly changes
in the Euro, British Pound Sterling, Canadian dollar, Swiss francs, Singapore dollars, Japanese Yen and Australian dollar. We seek to minimize
the impact of certain foreign currency fluctuations by hedging certain balance sheet exposures with foreign currency forward contracts. Any gain
or loss from settling these contracts is offset by the loss or gain derived from the underlying balance sheet exposures. The hedging contracts by
policy have maturities of less than three months. Additionally, by policy, we do not enter into any hedging contracts for trading or speculative
purposes.
Interest rate sensitivity
We had cash, cash equivalents and marketable securities totaling $1.8 billion at October 31, 2010. These amounts were invested primarily
in money market funds, time deposits, corporate notes and bonds, government securities and other debt securities with credit ratings of at least
single A or better. The cash, cash equivalents and short-term marketable securities are held for working capital purposes and were held for the
purchase of undeveloped land in San Francisco, California on November 1, 2010. Our investments are made for capital preservation purposes.
We do not enter into investments for trading or speculative purposes.
Our cash equivalents and our portfolio of marketable securities are subject to market risk due to changes in interest rates. Fixed rate interest
securities may have their market value adversely impacted due to a rise in interest rates, while floating rate securities may produce less income
than expected if interest rates fall. Due in part to these factors, our future investment income may fall short of expectation due to changes in
interest rates or we may suffer losses in principal if we are forced to sell securities that decline in the market value due to changes in interest
rates. However because we classify our debt securities as “available for sale,” no gains or losses are recognized due to changes in interest rates
unless such securities are sold prior to maturity or declines in fair value are determined to be other-than-temporary. Our fixed-
income portfolio is
subject to interest rate risk.
An immediate increase or decrease in interest rates of 100-basis points at October 31, 2010 could result in a $27.7 million market value
reduction or increase of the same amount. This estimate is based on a sensitivity model that measures market value changes when changes in
interest rates occur. Fluctuations in the value of our investment securities caused by a change in interest rates (gains or losses on the carrying
value) are recorded in other comprehensive income, and are realized only if we sell the underlying securities.
At January 31, 2010, we had cash, cash equivalents and marketable securities totaling $1.7 billion. The fixed-income portfolio was also
subject to interest rate risk. Changes in interest rates of 100-basis points would have resulted in market value changes of $13.1 million.
Market Risk and Market Interest Risk
In January 2010, we issued at par value $575.0 million of 0.75% convertible senior notes due 2015 (the “Notes”). Holders may convert
their Notes prior to maturity upon the occurrence of certain circumstances. Upon conversion, we would pay the holder an amount of cash equal
to the principal amount of the Notes. Amounts in excess of the principal amount, if any, may be paid in cash or stock at our option. Concurrent
with the issuance of the Notes, we entered into separate note hedges transactions and the sale of warrants. These separate transactions were
completed to reduce the potential economic dilution from the conversion of the Notes.
Our Notes have fixed annual interest rates at 0.75% and therefore, we do not have economic interest rate exposure on our Notes. However,
the value of the Notes are exposed to interest rate risk. Generally, the fair market value of our fixed interest rate Notes will increase as interest
rates fall and decrease as interest rates rise. In addition, the fair value of our Notes is affected by our stock price. The carrying value of our Notes
was $466.8 million as of October 31, 2010. This represents the liability component of the $575.0 million principal balance as
49
ITEM 3.
QUANTITATIVE AND QUALITATIVE DISCLOSURES ABOUT MARKET RISK

Table of Contents
of October 31, 2010. The total estimated fair value of our Notes at October 31, 2010 was $860.8 million and the fair value was determined based
on the closing trading price per $100 of our Notes as of the last day of trading for the third quarter of fiscal 2011, which was $149.70.
We have an investment portfolio that includes minority equity investments in several privately-held companies, many of which are in the
development stage. When our ownership interests are less than 20 percent and we do not have the ability to exert significant influence on the
investees, we account for the minority equity investments using the cost method of accounting. Otherwise, we account for the investments using
the equity method of accounting. At October 31, 2010, the net book value of these investments was $10.7 million.
(a) Evaluation of disclosure controls and procedures
Under the supervision and with the participation of our management, including our principal executive officer and principal financial
officer, we conducted an evaluation of the effectiveness of the design and operation of our disclosure controls and procedures, as defined in
Rules 13a-15(e) and 15d-15(e) under the Securities Exchange Act of 1934, as amended (the “Exchange Act”),
as of the end of the period covered
by this report (the “Evaluation Date”).
In designing and evaluating our disclosure controls and procedures, management recognizes that any disclosure controls and procedures,
no matter how well designed and operated, can provide only reasonable assurance of achieving the desired control objectives. In addition, the
design of disclosure controls and procedures must reflect the fact that there are resource constraints and that management is required to apply its
judgment in evaluating the benefits of possible controls and procedures relative to their costs.
Based on management’s evaluation, our chief executive officer and chief financial officer concluded that our disclosure controls and
procedures are designed to, and are effective to, provide assurance at a reasonable level that the information we are required to disclose in reports
that we file or submit under the Exchange Act is recorded, processed, summarized and reported within the time periods specified in Securities
and Exchange Commission rules and forms, and that such information is accumulated and communicated to our management, including our
chief executive officer and chief financial officer, as appropriate, to allow timely decisions regarding required disclosures.
(b) Changes in internal control over financial reporting
Under the supervision and with the participation of our management, including our principal executive officer and principal financial
officer, we conducted an evaluation of any changes in our internal control over financial reporting (as such term is defined in Rules 13a-15(f)
and 15d-15(f) under the Exchange Act) that occurred during our most recently completed fiscal quarter. Based on that evaluation, our principal
executive officer and principal financial officer concluded that there has not been any material change in our internal control over financial
reporting during the quarter covered by this report that materially affected, or is reasonably likely to materially affect, our internal control over
financial reporting.
50
ITEM 4.
CONTROLS AND PROCEDURES

Table of Contents
PART II. OTHER INFORMATION
We are involved in various legal proceedings arising from the normal course of business activities. In management’s opinion, resolution of
these matters is not expected to have a material adverse impact on our consolidated results of operations, cash flows or financial position.
However, depending on the nature and timing of any such dispute, an unfavorable resolution of a matter could materially affect our future results
of operations, cash flows or financial position.
On May 18, 2010, Microsoft Corporation filed a complaint against us in the United States District Court for the Western District of
Washington alleging infringement of nine patents which Microsoft claimed were related to certain aspects of our products and services. The
complaint sought, among other things, damages, attorneys’ fees and costs, and injunctive relief. On June 24, 2010, we filed a complaint against
Microsoft in the United States District Court for the District of Delaware alleging infringement of five of our patents related to certain aspects of
Microsoft’s products and services. The complaint sought, among other things, damages, attorneys’ fees and costs, and injunctive relief. On
August 2, 2010, we entered into a patent cross-license and settlement agreement with Microsoft and the companies subsequently dismissed their
respective cases.
Many of our subscription agreements require us to indemnify our customers for third-party intellectual property infringement claims,
which could increase the cost to us of an adverse ruling on such a claim. Any adverse determination related to intellectual property claims or
litigation could prevent us from offering our service to others, could be material to our net income or cash flows (or both) of a particular quarter
or could otherwise adversely affect our operating results.
The risks and uncertainties described below are not the only ones facing us. Other events that we do not currently anticipate or that we
currently deem immaterial also may affect our results of operations and financial condition.
Risks Related to Our Business and Industry
Defects or disruptions in our service could diminish demand for our service and subject us to substantial liability.
Because our service is complex and we have incorporated a variety of new computer hardware and software, both developed in-house and
acquired from third party vendors, our service may have errors or defects that users identify after they begin using it that could result in
unanticipated downtime for our subscribers and harm our reputation and our business. Internet-based services frequently contain undetected
errors when first introduced or when new versions or enhancements are released. We have from time to time found defects in our service and
new errors in our existing service may be detected in the future. In addition, our customers may use our service in unanticipated ways that may
cause a disruption in service for other customers attempting to access their data. Since our customers use our service for important aspects of
their business, any errors, defects, disruptions in service or other performance problems with our service could hurt our reputation and may
damage our customers’ businesses. If that occurs, customers could elect not to renew, or delay or withhold payment to us, we could lose future
sales or customers may make warranty or other claims against us, which could result in an increase in our provision for doubtful accounts, an
increase in collection cycles for accounts receivable or the expense and risk of litigation.
51
ITEM 1.
LEGAL PROCEEDINGS and CLAIMS
ITEM 1A.
RISK FACTORS

Table of Contents
Interruptions or delays in service from our third-party data center hosting facilities could impair the delivery of our service and harm
our business.
We currently serve our customers from third-
party data center hosting facilities located in the United States and Singapore. Any damage to,
or failure of, our systems generally could result in interruptions in our service. As we continue to add data centers and add capacity in our
existing data centers, we may move or transfer our data and our customers’ data. Despite precautions taken during this process, any unsuccessful
data transfers may impair the delivery of our service. Further, any damage to, or failure of, our systems generally could result in interruptions in
our service. Interruptions in our service may reduce our revenue, cause us to issue credits or pay penalties, cause customers to terminate their
subscriptions and adversely affect our renewal rates and our ability to attract new customers. Our business will also be harmed if our customers
and potential customers believe our service is unreliable.
As part of our current disaster recovery arrangements, our production environment and all of our customers’ data is currently replicated in
near real-time in a facility located on the east coast of the United States. Features added through acquisition are temporarily served through
alternate facilities. We do not control the operation of any of these facilities, and they are vulnerable to damage or interruption from earthquakes,
floods, fires, power loss, telecommunications failures and similar events. They may also be subject to break-ins, sabotage, intentional acts of
vandalism and similar misconduct. Despite precautions taken at these facilities, the occurrence of a natural disaster or an act of terrorism, a
decision to close the facilities without adequate notice or other unanticipated problems at these facilities could result in lengthy interruptions in
our service. Even with the disaster recovery arrangements, our service could be interrupted.
If our security measures are breached and unauthorized access is obtained to a customer’s data or our data or our information
technology systems, our service may be perceived as not being secure, customers may curtail or stop using our service and we may incur
significant legal and financial exposure and liabilities.
Our service involves the storage and transmission of customers’ proprietary information, and security breaches could expose us to a risk of
loss of this information, litigation and possible liability. These security measures may be breached as a result of third-party action, including
intentional misconduct by computer hackers, employee error, malfeasance or otherwise, during transfer of data to additional data centers or at
any time, and result in someone obtaining unauthorized access to our customers’ data or our data, including our intellectual property and other
confidential business information, or our information technology systems. Additionally, third parties may attempt to fraudulently induce
employees or customers into disclosing sensitive information such as user names, passwords or other information in order to gain access to our
customers’ data or our data, including our intellectual property and other confidential business information, or our information technology
systems. Because the techniques used to obtain unauthorized access, or to sabotage systems, change frequently and generally are not recognized
until launched against a target, we may be unable to anticipate these techniques or to implement adequate preventative measures. In addition, our
customers may authorize third party technology providers, whose applications are available through our AppExchange directory, to access their
customer data. Because we do not control the transmissions between our customers and third-party AppExchange technology providers, or the
processing of such data by third-party AppExchange technology providers, we cannot ensure the complete integrity or security of such
transmissions or processing. Any security breach could result in a loss of confidence in the security of our service, damage our reputation,
disrupt our business, lead to legal liability and negatively impact our future sales.
Because we recognize revenue from subscriptions for our service over the term of the subscription, downturns or upturns in sales may
not be immediately reflected in our operating results.
We generally recognize revenue from customers ratably over the terms of their subscription agreements, which are typically 12 to 24
months, although terms can range from one to 60 months. As a result, most of the revenue we report in each quarter is derived from the
recognition of deferred revenue relating to subscription agreements entered into during previous quarters. Consequently, a decline in new or
renewed subscriptions in
52

Table of Contents
any one quarter may not be immediately reflected in our revenue results for that quarter. Such a decline, however, will negatively affect our
revenue in future quarters. Accordingly, the effect of significant downturns in sales and market acceptance of our service, and potential changes
in our rate of renewals may not be fully reflected in our results of operations until future periods. Our subscription model also makes it difficult
for us to rapidly increase our revenue through additional sales in any period, as revenue from new customers must be recognized over the
applicable subscription term. In addition, we may be unable to adjust our cost structure to reflect the changes in revenues.
We cannot accurately predict subscription renewal or upgrade rates and the impact these rates may have on our future revenue and
operating results.
Our customers have no obligation to renew their subscriptions for our service after the expiration of their initial subscription period, which
is typically 12 to 24 months, and in fact, some customers have elected not to renew. In addition, our customers may renew for fewer
subscriptions, renew for shorter contract lengths, or renew for lower cost editions of our service. We cannot accurately predict renewal rates,
particularly for our enterprise customers who purchase a large number of subscriptions under multiyear contracts and for our small and medium
size business customers. Our renewal rates may decline or fluctuate as a result of a number of factors, including customer dissatisfaction with
our service, customers’ ability to continue their operations and spending levels, decreases in the number of users at our customers and
deteriorating general economic conditions. If our customers do not renew their subscriptions for our service or reduce the number of paying
subscriptions at the time of renewal, our revenue will decline and our business will suffer.
Our future success also depends in part on our ability to sell additional features and services, more subscriptions or enhanced editions of
our service to our current customers. This may also require increasingly sophisticated and costly sales efforts that are targeted at senior
management. Similarly, the rate at which our customers purchase new or enhanced services depends on a number of factors, including general
economic conditions. If our efforts to upsell to our customers are not successful, our business may suffer.
If we experience significant fluctuations in our rate of anticipated growth and fail to balance our expenses with our revenue forecasts,
our results could be harmed.
Due to our evolving business model, the unpredictability of new markets that we enter and the unpredictability of future general economic
and financial market conditions, we may not be able to accurately forecast our rate of growth. We plan our expense levels and investment on
estimates of future revenue and future anticipated rate of growth. We may not be able to adjust our spending quickly enough if the addition of
new subscriptions or the renewal rate for existing subscriptions falls short of our expectations.
As a result, we expect that our revenues, operating results and cash flows may fluctuate significantly on a quarterly basis. Our recent
revenue growth rates may not be sustainable and may decline in the future. We believe that period-to-period comparisons of our revenues,
operating results and cash flows may not be meaningful and should not be relied upon as an indication of future performance.
We have been and may in the future be sued by third parties for alleged infringement of their proprietary rights.
The software and Internet industries are characterized by the existence of a large number of patents, trademarks and copyrights and by
frequent litigation based on allegations of infringement or other violations of intellectual property rights. We have received in the past, and may
receive in the future, communications from third parties claiming that we have infringed the intellectual property rights of others. In addition, we
have been, and may in the future be, sued by third parties for alleged infringement of their proprietary rights, including patent infringement
lawsuits. Our technologies may be subject to injunction if they are held to infringe the rights of a third party and may not be able to withstand
any third-party claims against their use.
53

Table of Contents
The outcome of any litigation, regardless of its merits, is inherently uncertain. Any intellectual property claims and lawsuits could be time-
consuming and expensive to resolve, divert management attention from executing our business plan and require us to change our technology,
change our business practices and/or pay monetary damages or enter into short- or long-term royalty or licensing agreements. In addition, in
certain circumstances, such as those in which the opposing parties are large and well-funded companies, we may face a more expensive and
protracted path to resolution of such claims or lawsuits.
Many of our subscription agreements require us to indemnify our customers for third-party intellectual property infringement claims,
which would increase the cost to us of an adverse ruling on such a claim. Any adverse determination related to intellectual property claims or
litigation could prevent us from offering our service to others, could be material to our net income or cash flows (or both) of a particular quarter
or could otherwise adversely affect our operating results.
Our exposure to risks associated with the use of intellectual property may be increased as a result of acquisitions, as we have a lower level
of visibility into the development process with respect to such technology or the care taken to safeguard against infringement risks. In addition,
third parties may make infringement and similar or related claims after we have acquired technology that had not been asserted prior to our
acquisition.
Our quarterly results can fluctuate and our stock price and the value of your investment could decline substantially.
Our quarterly operating results are likely to fluctuate. For example, our fourth quarter has historically been our strongest quarter for new
business and renewals. The year-over-year compounding effect of this seasonality in billing patterns and overall new business and renewal
activity causes the value of invoices that we generate in the fourth quarter to continually increase in proportion to our billings in the other three
quarters of our fiscal year.
Additionally, some of the important factors that may cause our revenues, operating results and cash flows to fluctuate from quarter to
quarter include:
54
•
our ability to retain and increase sales to existing customers, attract new customers and satisfy our customers
’
requirements;
•
the renewal rates for our service;
•
the amount and timing of operating costs and capital expenditures related to the operations and expansion of our business;
•
the number of new employees added;
•
changes in our pricing policies whether initiated by us or as a result of intense competition;
•
the cost, timing and management effort for the introduction of new features to our service;
•
the rate of expansion and productivity of our sales force;
•
the length of the sales cycle for our service;
•
new product and service introductions by our competitors;
•
our success in selling our service to large enterprises;
•
variations in the revenue mix of editions of our service;
•
technical difficulties or interruptions in our service;
•
expenses related to developing our new global headquarters and increasing our data center capacity and expanding our data centers
domestically and internationally;
•
changes in foreign currency exchange rates;

Table of Contents
Many of these factors are not within our control, and the occurrence of one or more of them might cause our operating results to vary
widely. As such, we believe that quarter-to-quarter comparisons of our revenues, operating results and cash flows may not be meaningful and
should not be relied upon as an indication of future performance.
Additionally, we may also fail to meet or exceed the expectations of securities analysts or investors, and the market price of our common
stock. Moreover, our stock price may be based on expectations of our future performance that may be unrealistic or that may not be met.
Weakened global economic conditions may adversely affect our industry, business and results of operations.
Our overall performance depends in part on worldwide economic conditions. The United States and other key international economies
have been impacted by falling demand for a variety of goods and services, restricted credit, going concern threats to major multinational
companies and medium and small businesses, poor liquidity, reduced corporate profitability, volatility in credit, equity and foreign exchange
markets, bankruptcies and overall uncertainty with respect to the economy. These conditions affect the rate of information technology spending
and could adversely affect our customers’ ability or willingness to purchase our enterprise cloud computing application service, delay
prospective customers’ purchasing decisions, reduce the value or duration of their subscription contracts, or affect renewal rates, all of which
could adversely affect our operating results.
As we acquire companies or technologies in the future, they could prove difficult to integrate, disrupt our business, dilute stockholder
value and adversely affect our operating results and the value of your investment.
As part of our business strategy, we regularly evaluate investments in, or acquisitions of, complementary businesses, joint ventures,
services and technologies, and we expect that periodically we will continue to make such investments and acquisitions in the future. Acquisitions
and investments involve numerous risks, including:
55
•
changes in interest rates and our mix of investments, which would impact our return on our investments in cash and marketable
securities;
•
conditions, particularly sudden changes, in the financial markets have and may continue to impact the value of and access to our
investment portfolio;
•
changes in the effective tax rates;
•
general economic conditions that may adversely affect either our customers’ ability or willingness to purchase additional subscriptions
or upgrade their service, or delay a prospective customers’ purchasing decision, or reduce the value of new subscription contracts, or
affect renewal rates;
•
timing of additional investments in our enterprise cloud computing application service and in our consulting service;
•
changes in deferred revenue balances due to the seasonal nature of our customer invoicing, changes in the average duration of our
invoices, rate of renewals and the rate of new business growth;
•
regulatory compliance costs;
•
the timing of customer payments and payment defaults by customers;
•
costs associated with acquisitions of companies and technologies;
•
extraordinary expenses such as litigation or other dispute
-
related settlement payments;
•
the impact of new accounting pronouncements; and
•
the timing of stock awards to employees and the related adverse financial statement impact of having to expense those stock awards
ratably over their vesting schedules.
•
the potential failure to achieve the expected benefits of the combination or acquisition;

Table of Contents
In addition, if we finance acquisitions by issuing equity or convertible debt securities, our existing stockholders may be diluted which
could affect the market price of our common stock. Further, if we fail to properly evaluate and execute acquisitions or investments, our business
and prospects may be seriously harmed and the value of your investment may decline.
We rely on third-party computer hardware and software that may be difficult to replace or which could cause errors or failures of our
service.
We rely on computer hardware purchased or leased and software licensed from third parties in order to offer our service, including
database software from Oracle Corporation. This hardware and software may not continue to be available at reasonable prices or on
commercially reasonable terms, or at all. Any loss of the right to use any of this hardware or software could significantly increase our expenses
and otherwise result in delays in the provisioning of our service until equivalent technology is either developed by us, or, if available, is
identified, obtained and integrated, which could harm our business. Any errors or defects in third-party hardware or software could result in
errors or a failure of our service which could harm our business.
If the market for our technology delivery model and an enterprise cloud computing application service develops more slowly than we
expect, our business could be harmed.
The market for enterprise cloud computing application services is not as mature as the market for packaged enterprise software, and it is
uncertain whether these services will achieve and sustain high levels of demand and market acceptance. Our success will depend to a substantial
extent on the willingness of enterprises, large and small, to increase their use of enterprise cloud computing application services in general, and
for CRM in particular. Many enterprises have invested substantial personnel and financial resources to integrate traditional enterprise software
into their businesses, and therefore may be reluctant or unwilling to migrate to an enterprise cloud computing application service. Furthermore,
some enterprises may be reluctant or unwilling to use
56
•
difficulties in and the cost of integrating operations, technologies, services and personnel;
•
diversion of financial and managerial resources from existing operations;
•
risk of entering new markets in which we have little or no experience or where competitors may have stronger market positions;
•
potential write
-
offs of acquired assets or investments;
•
potential loss of key employees;
•
inability to generate sufficient revenue to offset acquisition or investment costs;
•
the inability to maintain relationships with customers and partners of the acquired business;
•
the difficulty of incorporating acquired technology and rights into our products and services and of maintaining quality standards
consistent with our brand;
•
potential unknown liabilities associated with the acquired businesses;
•
unanticipated expenses related to acquired technology and its integration into existing technology;
•
negative impact to our results of operations because of the depreciation and amortization of amounts related to acquired intangible
assets, fixed assets and deferred compensation, and the loss of acquired deferred revenue;
•
delays in customer purchases due to uncertainty related to any acquisition;
•
the need to implement controls, procedures and policies appropriate for a public company at companies that prior to the acquisition
lacked such controls, procedures and policies; and
•
challenges caused by distance, language and cultural differences.

Table of Contents
enterprise cloud computing application services because they have concerns regarding the risks associated with security capabilities, among
other things, of the technology delivery model associated with these services. If enterprises do not perceive the benefits of enterprise cloud
computing application services, then the market for these services may not develop at all, or it may develop more slowly than we expect, either
of which would significantly adversely affect our operating results. In addition, we may make errors in predicting and reacting to relevant
business trends, which could harm our business. Our success also depends on the willingness of third-party developers to build applications that
are complementary to our service. Without the development of these applications, both current and potential customers may not find our service
sufficiently attractive. In addition, for those customers who authorize third-party technology partners access to their data, we do not warrant the
functionality, security and integrity of the data transmission or processing. Despite contract provisions to protect us, customers may look to us to
support and warrant the third-party applications, which may expose us to potential claims, liabilities and obligations for applications we did not
develop or sell.
The market in which we participate is intensely competitive, and if we do not compete effectively, our operating results could be
harmed.
The market for enterprise CRM business applications and development platforms is highly competitive, rapidly evolving and fragmented,
and subject to changing technology, shifting customer needs and frequent introductions of new products and services. We compete primarily
with vendors of packaged CRM software, whose software is installed by the customer directly, and companies offering on-demand CRM
applications. We also compete with internally developed applications and face, or expect to face, competition from enterprise software vendors
and online service providers who may develop toolsets and products that allow customers to build new applications that run on the customers’
current infrastructure or as hosted services. Our current competitors include:
Many of our current and potential competitors enjoy substantial competitive advantages, such as greater name recognition, longer
operating histories and larger marketing budgets, as well as substantially greater financial, technical and other resources. In addition, many of
our current and potential competitors have established marketing relationships and access to larger customer bases, and have major distribution
agreements with consultants, system integrators and resellers.
As a result, our competitors may be able to respond more quickly and effectively than we can to new or changing opportunities,
technologies, standards or customer requirements. Furthermore, because of these advantages, even if our service is more effective than the
products that our competitors offer, potential customers might accept competitive products and services in lieu of purchasing our service. For all
of these reasons, we may not be able to compete successfully against our current and future competitors.
Our efforts to expand our service beyond the CRM market may not succeed and may reduce our revenue growth rate.
We derive substantially all of our revenue from subscriptions to our CRM enterprise cloud computing application service, and we expect
this will continue for the foreseeable future. The market for our Force.com cloud computing platform is new and it is uncertain whether our
efforts will ever result in significant revenue for us. Further, the introduction of new services beyond the CRM market may not be successful,
and early stage interest and adoption of such new services may not result in long term success or significant revenue for us. Our efforts to expand
our service beyond the CRM market may not succeed and may reduce our revenue growth rate.
57
•
enterprise software application vendors;
•
on
-
demand CRM application service providers;
•
enterprise application service providers;
•
traditional platform development environment companies; and
•
cloud computing development platform companies.

Table of Contents
Supporting our existing and growing customer base could strain our personnel resources and infrastructure, and if we are unable to
scale our operations and increase productivity, we may not be able to successfully implement our business plan.
We continue to experience significant growth in our customer base, which has placed a strain on our management, administrative,
operational and financial infrastructure. We anticipate that additional investments in our infrastructure and research and development spending
will be required to scale our operations and increase productivity, to address the needs of our customers, to further develop and enhance our
service, and to expand into new geographic areas.
Our success will depend in part upon the ability of our senior management to manage our projected growth effectively. To do so, we must
continue to increase the productivity of our existing employees and to hire, train and manage new employees as needed. To manage the expected
domestic and international growth of our operations and personnel, we will need to continue to improve our operational, financial and
management controls and our reporting systems and procedures. The additional investments we are making will increase our cost base, which
will make it more difficult for us to offset any future revenue shortfalls by reducing expenses in the short term. If we fail to successfully scale
our operations and increase productivity, we will be unable to execute our business plan.
As more of our sales efforts are targeted at larger enterprise customers, our sales cycle may become more time-consuming and
expensive, we may encounter pricing pressure and implementation challenges, and we may have to delay revenue recognition for some
complex transactions, all of which could harm our business and operating results.
As we target more of our sales efforts at larger enterprise customers, we will face greater costs, longer sales cycles and less predictability in
completing some of our sales. In this market segment, the customer’s decision to use our service may be an enterprise-wide decision and, if so,
these types of sales would require us to provide greater levels of education regarding the use and benefits of our service, as well as education
regarding privacy and data protection laws and regulations to prospective customers with international operations. In addition, larger customers
may demand more customization, integration services and features. As a result of these factors, these sales opportunities may require us to
devote greater sales support and professional services resources to individual customers, driving up costs and time required to complete sales and
diverting sales and professional services resources to a smaller number of larger transactions, while potentially requiring us to delay revenue
recognition on some of these transactions until the technical or implementation requirements have been met.
Periodic restructurings of our sales organization can be disruptive and may negatively impact our revenues.
We periodically restructure or make other adjustments to our sales organization in response to market opportunities, competitive threats,
management changes, product introductions or enhancements, sales performance, increases in sales headcount, cost levels, and other internal and
external considerations. In the past, these restructurings sometimes resulted in a temporary lack of focus and reduced productivity; these effects
could recur in connection with any future sales restructurings we might undertake and our rate of revenue growth could be negatively affected.
If we are not able to develop enhancements and new features to our existing service or acceptable new services that keep pace with
technological developments, our business will be harmed.
If we are unable to develop enhancements to and new features for our existing service or acceptable new services that keep pace with rapid
technological developments, our business will be harmed. The success of enhancements, new features and services depends on several factors,
including the timely completion, introduction and market acceptance of the feature or edition. Failure in this regard may significantly impair our
58

Table of Contents
revenue growth. In addition, because our service is designed to operate on a variety of network hardware and software platforms using a standard
browser, we will need to continuously modify and enhance our service to keep pace with changes in Internet-related hardware, software,
communication, browser and database technologies. We may not be successful in either developing these modifications and enhancements or in
timely bringing them to market. Furthermore, uncertainties about the timing and nature of new network platforms or technologies, or
modifications to existing platforms or technologies, could increase our research and development expenses. Any failure of our service to operate
effectively with future network platforms and technologies could reduce the demand for our service, result in customer dissatisfaction and harm
our business.
Our business could be adversely affected if our customers are not satisfied with implementation and customization services provided by
us or our partners.
Our business depends on our ability to satisfy our customers, both with respect to our CRM service and platform and the professional
services that customize our CRM service and platform to meet our customers’ business needs. Professional services may be performed by our
own staff, or by a third party or a combination of the two. Our strategy is to work with third parties to increase the breadth of capability and
depth of capacity for delivery of these services to our customers. If a customer is not satisfied with the quality of work performed by us or a third
party or with the type of services or solutions delivered, then we could incur additional costs to address the situation, the profitability of that
work might be impaired, and the customer’s dissatisfaction with our services could damage our ability to obtain additional work from that
customer. In addition, negative publicity related to our customer relationships, regardless of its accuracy, may further damage our business by
affecting our ability to compete for new business with current and prospective customers.
Any failure to protect our intellectual property rights could impair our ability to protect our proprietary technology and our brand.
If we fail to protect our intellectual property rights adequately, our competitors might gain access to our technology, and our business
might be harmed. In addition, defending our intellectual property rights might entail significant expense. Any of our trademarks or other
intellectual property rights may be challenged by others or invalidated through administrative process or litigation. While we have a few U.S.
patents and many U.S. and international patent applications pending, we may be unable to obtain patent protection for the technology covered in
our patent applications. In addition, our existing patents and any patents issued in the future may not provide us with competitive advantages, or
may be successfully challenged by third parties. Furthermore, legal standards relating to the validity, enforceability and scope of protection of
intellectual property rights are uncertain. Effective patent, trademark, copyright and trade secret protection may not be available to us in every
country in which our service is available. The laws of some foreign countries may not be as protective of intellectual property rights as those in
the U.S., and mechanisms for enforcement of intellectual property rights may be inadequate. Accordingly, despite our efforts, we may be unable
to prevent third parties from infringing upon or misappropriating our intellectual property.
We might be required to spend significant resources to monitor and protect our intellectual property rights. We may initiate claims or
litigation against third parties for infringement of our proprietary rights or to establish the validity of our proprietary rights. Any litigation,
whether or not it is resolved in our favor, could result in significant expense to us and divert the efforts of our technical and management
personnel.
If we fail to develop our brands, our business may suffer.
We believe that developing and maintaining awareness of the salesforce.com brand and our other brands is critical to achieving widespread
acceptance of our existing and future services and is an important element in attracting new customers. In the past, our efforts to build our brands
have involved significant expense. Brand promotion activities may not yield increased revenue, and even if they do, any increased revenue may
not offset the expenses we incurred in building our brands. If we fail to successfully promote and maintain our brands, or
59

Table of Contents
incur substantial expenses in an unsuccessful attempt to promote and maintain our brands, we may fail to attract enough new customers or retain
our existing customers to the extent necessary to realize a sufficient return on our brand-building efforts, and our business could suffer.
We may not realize the anticipated benefits in connection with our purchase of undeveloped land in San Francisco where we plan to
develop our global headquarters. If we do not realize these benefits, our financial performance will be negatively impacted.
In November 2010, we paid $278.0 million in cash for approximately 14 acres of undeveloped real estate in San Francisco, California
which we plan to develop into our global headquarters. We may not realize the anticipated benefits with respect to the purchase and future
development of such real estate. We have devoted significant capital resources to the purchase, and we will be required to devote additional
resources in the future to building our global headquarters on such land, which may impact our liquidity and financial flexibility. We may not be
able to obtain financing for development projects on favorable terms, or at all, or complete construction on schedule or within budget. Any delay
or lack of available financing could result in increased constructions costs and debt costs to fund such construction and development. In addition,
our development efforts will otherwise be subject to various operational risks. We may not be able to obtain, or may experience delays in
obtaining, all necessary zoning, land-use, building, occupancy and other governmental permits and authorizations. The construction costs and
total investment amounts may exceed any estimates that we formulate, and projects may not be completed, or delivered as planned. Finally, real
estate assets are not as liquid as certain other types of assets. In the event that we have a future need to sell this property, we may not be able to
do so on favorable terms or at all.
Sales to customers outside the United States expose us to risks inherent in international sales.
Because we sell our service throughout the world, we are subject to risks and challenges that we would otherwise not face if we conducted
our business only in the United States. For example, sales in Europe and Asia Pacific together represented approximately 30 percent of our total
revenues for the year ended January 31, 2010, and we intend to continue to expand our international sales efforts. The risks and challenges
associated with sales to customers outside the United States include:
60
•
localization of our service, including translation into foreign languages and associated expenses;
•
laws and business practices favoring local competitors;
•
compliance with multiple, conflicting and changing governmental laws and regulations, including employment, tax, privacy and data
protection laws and regulations;
•
treatment of revenue from international sources and changes to tax codes, including being subject to foreign tax laws and being liable
for paying withholding income or other taxes in foreign jurisdictions;
•
regional data privacy laws that apply to the transmission of our customers
’
data across international borders;
•
foreign currency fluctuations and controls;
•
different pricing environments;
•
difficulties in staffing and managing foreign operations;
•
different or lesser protection of our intellectual property;
•
longer accounts receivable payment cycles and other collection difficulties;
•
regional economic conditions; and
•
regional political conditions.

Table of Contents
Any of these factors could negatively impact our business and results of operations.
Additionally, our international subscription fees are paid either in U.S. dollars or local currency. As a result, fluctuations in the value of the
U.S. dollar and foreign currencies may make our service more expensive for international customers, which could harm our business.
Evolving regulation of the Internet may affect us adversely.
As Internet commerce continues to evolve, increasing regulation by federal, state or foreign agencies becomes more likely. For example,
we believe increased regulation is likely in the area of data privacy, and laws and regulations applying to the solicitation, collection, processing
or use of personal or consumer information could affect our customers’ ability to use and share data, potentially reducing demand for CRM
solutions and restricting our ability to store, process and share data with our customers. In addition, taxation of services provided over the
Internet or other charges imposed by government agencies or by private organizations for accessing the Internet may also be imposed. Any
regulation imposing greater fees for Internet use or restricting information exchange over the Internet could result in a decline in the use of the
Internet and the viability of Internet-based services, which could harm our business.
Privacy concerns and laws or other domestic or foreign regulations may reduce the effectiveness of our solution and adversely affect
our business.
Our customers can use our service to store contact and other personal or identifying information regarding their customers and contacts.
Federal, state and foreign government bodies and agencies have adopted or are considering adopting laws and regulations regarding the
collection, use and disclosure of personal information obtained from consumers and individuals. The costs of compliance with, and other
burdens imposed by, such laws and regulations that are applicable to the businesses of our customers may limit the use and adoption of our
service and reduce overall demand for it, or lead to significant fines, penalties or liabilities for any noncompliance with such privacy laws.
Furthermore, privacy concerns may cause our customers’
customers to resist providing the personal data necessary to allow our customers to use
our service effectively. Even the perception of privacy concerns, whether or not valid, may inhibit market adoption of our service in certain
industries.
For example, in the United States regulations such as the Gramm-Leach-Bliley Act, which protects and restricts the use of consumer credit
and financial information, and the Health Insurance Portability and Accountability Act of 1996, which regulates the use and disclosure of
personal health information, impose significant requirements and obligations on businesses that may affect the use and adoption of our service.
The European Union has also adopted a data privacy directive that requires member states to impose restrictions on the collection and use of
personal data that, in some respects, are far more stringent, and impose more significant burdens on subject businesses, than current privacy
standards in the United States.
All of these domestic and international legislative and regulatory initiatives may adversely affect our customers’ ability to collect and/or
use demographic and personal information from their customers, which could reduce demand for our service. Many other jurisdictions have
similar stringent privacy laws and regulations.
In addition to government activity, privacy advocacy groups and the technology and other industries are considering various new,
additional or different self-regulatory standards that may place additional burdens on us. If the gathering of personal information were to be
curtailed in this manner, CRM solutions would be less effective, which may reduce demand for our service and harm our business.
61

Table of Contents
We are dependent on our management team and development and operations personnel, and the loss of one or more key employees or
groups could harm our business and prevent us from implementing our business plan in a timely manner.
Our success depends substantially upon the continued services of our executive officers and other key members of management,
particularly our Chief Executive Officer. From time to time, there may be changes in our executive management team resulting from the hiring
or departure of executives. Such changes in our executive management team may be disruptive to our business. We are also substantially
dependent on the continued service of our existing development and operations personnel because of the complexity of our service and
technologies. We do not have employment agreements with any of our executive officers, key management, development or operations
personnel and, therefore, they could terminate their employment with us at any time. We do not maintain key person life insurance policies on
any of our employees. The loss of one or more of our key employees or groups could seriously harm our business.
Because competition for our target employees is intense, we may not be able to attract and retain the highly skilled employees we need
to support our operations and growing customer base.
In the technology industry, there is substantial and continuous competition for engineers with high levels of experience in designing,
developing and managing software and Internet-related services, as well as competition for sales executives and operations personnel. We may
not be successful in attracting and retaining qualified personnel. We have from time to time experienced, and we expect to continue to
experience, difficulty in hiring and retaining highly skilled employees with appropriate qualifications. In addition, job candidates and existing
employees often consider the value of the stock awards they receive in connection with their employment. If our stock price performs poorly, it
may adversely affect our ability to retain highly skilled employees. In addition, since we expense all stock-based compensation, we may
periodically change our stock compensation practices, which may include reducing the number of employees eligible for options or reducing the
size of equity awards granted per employee. If we fail to attract new personnel or fail to retain and motivate our current personnel, our business
and future growth prospects could be severely harmed.
Our business is subject to changing regulations regarding corporate governance and public disclosure that have increased both our
costs and the risk of non-compliance.
We are subject to rules and regulations by various governing bodies, including, for example, the Securities and Exchange Commission,
which are charged with the protection of investors and the oversight of companies whose securities are publicly traded. Our efforts to comply
with new and changing regulations have resulted in and are likely to continue to result in, increased general and administrative expenses and a
diversion of management time and attention from revenue-generating activities to compliance activities.
Moreover, because these laws, regulations and standards are subject to varying interpretations, their application in practice may evolve
over time as new guidance becomes available. This evolution may result in continuing uncertainty regarding compliance matters and additional
costs necessitated by ongoing revisions to our disclosure and governance practices. If we fail to address and comply with these regulations and
any subsequent changes, our business may be harmed.
Unanticipated changes in our effective tax rate could adversely affect our future results.
We are subject to income taxes in the United States and various foreign jurisdictions, and our domestic and international tax liabilities are
subject to the allocation of expenses in differing jurisdictions.
Our effective tax rate could be adversely affected by changes in the mix of earnings and losses in countries with differing statutory tax
rates, certain non-deductible expenses as a result of acquisitions, the valuation of deferred tax assets and liabilities and changes in federal, state
or international tax laws and accounting principles. Increases in our effective tax rate could materially affect our net results.
62

Table of Contents
In addition, we are subject to income tax audits by many tax jurisdictions throughout the world. Although we believe our income tax
liabilities are reasonably estimated and accounted for in accordance with applicable laws and principles, an adverse resolution of one or more
uncertain tax positions in any period could have a material impact on the results of operations for that period.
Natural disasters and other events beyond our control could materially adversely affect us.
Natural disasters or other catastrophic events may cause damage or disruption to our operations, international commerce and the global
economy, and thus could have a strong negative effect on us. Our business operations are subject to interruption by natural disasters, fire, power
shortages, pandemics and other events beyond our control. Although we maintain crisis management and disaster response plans, such events
could make it difficult or impossible for us to deliver our services to our customers, and could decrease demand for our services. The majority of
our research and development activities, corporate headquarters, information technology systems, and other critical business operations, are
located near major seismic faults in the San Francisco Bay Area. Because we do not carry earthquake insurance for direct quake-related losses,
and significant recovery time could be required to resume operations, our financial condition and operating results could be materially adversely
affected in the event of a major earthquake or catastrophic event.
Risks Relating to Ownership of Our Common Stock and our Convertible Senior Notes due 2015
The market price of our common stock is likely to be volatile and could subject us to litigation.
The trading prices of the securities of technology companies have been highly volatile. Accordingly, the market price of our common stock
has been and is likely to continue to be subject to wide fluctuations. Factors affecting the market price of our common stock include:
63
•
variations in our operating results, earnings per share, cash flows from operating activities, deferred revenue, and other financial
metrics and non
-
financial metrics, and how those results compare to analyst expectations;
•
forward looking guidance to industry and financial analysts related to future revenue and earnings per share;
•
the net increases in the number of customers, either independently or as compared with published expectations of industry, financial or
other analysts that cover our company;
•
changes in the estimates of our operating results or changes in recommendations by securities analysts that elect to follow our common
stock;
•
announcements of technological innovations, new services or service enhancements, strategic alliances or significant agreements by us
or by our competitors;
•
announcements by us or by our competitors of mergers or other strategic acquisitions, or rumors of such transactions involving us or
our competitors;
•
announcements of customer additions and customer cancellations or delays in customer purchases;
•
recruitment or departure of key personnel;
•
disruptions in our service due to computer hardware, software or network problems;
•
the economy as a whole, market conditions in our industry, and the industries of our customers;
•
trading activity by a limited number of stockholders who together beneficially own a majority of our outstanding common stock; and
•
any other factors discussed herein.

Table of Contents
In addition, if the market for technology stocks or the stock market in general experiences uneven investor confidence, the market price of
our common stock could decline for reasons unrelated to our business, operating results or financial condition. The market price of our common
stock might also decline in reaction to events that affect other companies within, or outside, our industry even if these events do not directly
affect us. Some companies that have experienced volatility in the trading price of their stock have been the subject of securities class action
litigation. If we are the subject of such litigation, it could result in substantial costs and a diversion of management’s attention and resources.
The concentration of our capital stock ownership with insiders will likely limit your ability to influence corporate matters.
Our executive officers, directors, and several stockholders and their affiliated entities together beneficially own a majority of our
outstanding common stock. As a result, these stockholders, if they act together or in a block, could have significant influence over most matters
that require approval by our stockholders, including the election of directors and approval of significant corporate transactions, even if other
stockholders oppose them. This concentration of ownership might also have the effect of delaying or preventing a change of control of our
company that other stockholders may view as beneficial.
Provisions in our amended and restated certificate of incorporation and bylaws and Delaware law might discourage, delay or prevent a
change of control of our company or changes in our management and, therefore, depress the market price of our common stock.
Our amended and restated certificate of incorporation and bylaws contain provisions that could depress the market price of our common
stock by acting to discourage, delay or prevent a change in control of our company or changes in our management that the stockholders of our
company may deem advantageous. These provisions among other things:
In addition, Section 203 of the Delaware General Corporation Law may discourage, delay or prevent a change in control of our company.
Section 203 imposes certain restrictions on merger, business combinations and other transactions between us and holders of 15 percent or more
of our common stock.
Our debt service obligations may adversely affect our financial condition and cash flows from operations.
As a result of our sale of $575.0 million of 0.75 percent convertible senior notes in January 2010 (the “Notes”), we now have long-term
debt that we have not had to maintain in the past.
64
•
establish a classified board of directors so that not all members of our board are elected at one time;
•
permit the board of directors to establish the number of directors;
•
provide that directors may only be removed
“
for cause
”
and only with the approval of 66 2/3 percent of our stockholders;
•
require super
-
majority voting to amend some provisions in our amended and restated certificate of incorporation and bylaws;
•
authorize the issuance of
“
blank check
”
preferred stock that our board could use to implement a stockholder rights plan (also known as
a
“
poison pill
”
);
•
eliminate the ability of our stockholders to call special meetings of stockholders;
•
prohibit stockholder action by written consent, which requires all stockholder actions to be taken at a meeting of our stockholders;
•
provide that the board of directors is expressly authorized to make, alter or repeal our bylaws; and
•
establish advance notice requirements for nominations for election to our board or for proposing matters that can be acted upon by
stockholders at annual stockholder meetings.

Table of Contents
Our maintenance of indebtedness could have important consequences because:
Our ability to meet our expenses and debt obligations will depend on our future performance, which will be affected by financial, business,
economic, regulatory and other factors. We will not be able to control many of these factors, such as economic conditions and governmental
regulations. Our operations may not generate sufficient cash to enable us to service our debt. If we fail to make a payment on our debt, we could
be in default on such debt.
We expect that the trading price of the Notes will be significantly affected by the market price of our common stock, which may be
volatile, the general level of interest rates and our credit quality.
The market price of our common stock, as well as the general level of interest rates and our credit quality, will likely significantly affect
the trading price of the Notes. Our common stock has experienced significant price and volume fluctuations.
We cannot predict whether the market price of our common stock will rise or fall. The market price of our common stock will be
influenced by a number of factors, including general market conditions, variations in our operating results, earnings per share, cash flows,
deferred revenue, other financial and non-financial metrics and other factors described in greater detail elsewhere in this section, many of which
are beyond our control.
The market price of our common stock also could be affected by possible sales of common stock by investors who view the Notes as an
attractive means of equity participation in us and by hedging or arbitrage activity involving our common stock that we expect to develop as a
result of the issuance of the Notes. The hedging or arbitrage activity could, in turn, affect the trading prices of the Notes.
We also cannot predict whether interest rates will rise or fall. During the term of the Notes, interest rates will be influenced by a number of
factors, most of which are beyond our control. However, if interest rates increase, the option value of the Notes’ convertibility feature will
increase, but the yield of the Notes will decrease, and if interest rates decrease, the option value of the Notes’
convertibility feature will decrease,
but the yield of the notes will increase.
In addition, our credit quality may vary substantially during the term of the Notes and will be influenced by a number of factors, including
variations in our cash flows and the amount of indebtedness we have outstanding. Any decrease in our credit quality could negatively impact the
trading price of the Notes.
We may issue additional shares of our common stock or instruments convertible into shares of our common stock, including in
connection with the conversion of the Notes, and thereby materially and adversely affect the market price of our common stock and the
trading price of the Notes.
We are not restricted from issuing additional shares of our common stock or other instruments convertible into, or exchangeable or
exercisable for, shares of our common stock during the life of the Notes. If we issue additional shares of our common stock or instruments
convertible into shares of our common stock, it may materially and adversely affect the market price of our common stock and, in turn, the
trading price of the Notes.
In addition, the conversion of some or all of the Notes may dilute the ownership interests of existing holders of our common stock, and any
sales in the public market of any shares of our common stock issuable upon such conversion of the notes could adversely affect the prevailing
market price of our common stock. In addition, the anticipated conversion of the Notes could depress the market price of our common stock.
65
•
it may impair our ability to obtain additional financing in the future;
•
an increased portion of our cash flows from operations may have to be dedicated towards repaying the principal in 2015;
•
it may make us more vulnerable to downturns in our business, our industry or the economy in general.

Table of Contents
The Notes and the indenture that will govern the Notes contain limited protections against certain types of important corporate events
and may not protect your investment upon the occurrence of such corporate events and will not protect your investment upon the occurrence
of other corporate events.
The indenture for the Notes does not:
Furthermore, the indenture for the Notes contains only limited protections in the event of a change in control. We could engage in many
types of transactions, such as certain acquisitions, refinancings or recapitalizations, that could substantially affect our capital structure and the
value of the Notes and our common stock, but would not constitute a “fundamental change” that permits holders to require us to purchase their
Notes under the indenture.
We may not have the ability to raise the funds necessary to re-pay the Notes.
There can be no assurance that we will have sufficient financial resources, or will be able to arrange financing, to pay the fundamental
change purchase price if holders submit their Notes for purchase by us upon the occurrence of a fundamental change or to pay the amount of
cash due if holders surrender their Notes for conversion. In addition, agreements governing any future debt may restrict our ability to make each
of the required cash payments even if we have sufficient funds to make them. Furthermore, our ability to purchase the Notes or to pay cash upon
the conversion of the Notes may be limited by law or regulatory authority. In addition, if we fail to purchase the Notes, to pay interest due on, or
to pay the amount of cash due upon conversion, we will be in default under the indenture. Our inability to pay for the Notes that are tendered for
purchase or upon conversion could result in receiving substantially less than the principal amount of the Notes.
The fundamental change provisions may delay or prevent an otherwise beneficial takeover attempt of us.
The fundamental change purchase rights, which will allow note holders to require us to purchase all or a portion of their Notes upon the
occurrence of a fundamental change and the provisions requiring an increase to the conversion rate for conversions in connection with a make-
whole fundamental change may in certain circumstances delay or prevent a takeover of us and the removal of incumbent management that might
otherwise be beneficial to investors.
66
•
require us to maintain any financial ratios or specific levels of net worth, revenues, income, cash flows or liquidity;
•
protect holders of the Notes in the event that we experience significant adverse changes in our financial condition or results of
operations;
•
limit our subsidiaries’ ability to incur indebtedness that would effectively rank senior to the Notes to the extent of the value of the
assets securing the indebtedness;
•
limit our ability to incur indebtedness that is equal in right of payment to the Notes;
•
limit our ability to incur indebtedness with a maturity date earlier than the maturity date of the Notes;
•
restrict our subsidiaries
’
ability to issue securities or incur liability that would be structurally senior to our indebtedness;
•
restrict our ability to purchase or prepay our securities; or
•
restrict our ability to make investments or to purchase or pay dividends or make other payments in respect of our common stock or
other securities ranking junior to the Notes.

Table of Contents
The convertible note hedge and warrant transactions may affect the trading price of the Notes and the market price of our common
stock.
We entered into privately negotiated convertible note hedge transactions with the hedge counterparties concurrently with the issuance of
the Notes. We also entered into privately negotiated warrant transactions with the hedge counterparties. Taken together, the convertible note
hedge transactions and the warrant transactions are expected, but not guaranteed, to reduce the potential dilution with respect to our common
stock upon conversion of the Notes.
As the hedge counterparties and their respective affiliates modify their hedge positions from time to time by entering into or unwinding
various over-the-counter derivative transactions with respect to our common stock, and/or by purchasing or selling shares of our common stock
or the Notes in privately negotiated transactions and/ or open market transactions, their activities could adversely affect the market price of our
common stock and the trading price of the Notes.
We are subject to counterparty risk with respect to the convertible note hedge transactions.
The hedge counterparties are financial institutions or affiliates of financial institutions, and we will be subject to the risk that these hedge
counterparties may default under the convertible note hedge transactions. Our exposure to the credit risk of the hedge counterparties will not be
secured by any collateral. Recent global economic conditions have resulted in the actual or perceived failure or financial difficulties of many
financial institutions. If one or more of the hedge counterparties to one or more of our convertible note hedge transactions becomes subject to
insolvency proceedings, we may become an unsecured creditor in those proceedings with a claim equal to our exposure at the time under those
transactions. Our exposure will depend on many factors but, generally, the increase in our exposure will be correlated to the increase in our stock
price and in the volatility of our stock. In addition, upon a default by one of the hedge counterparties, we may suffer adverse tax consequences
and dilution with respect to our common stock. We can provide no assurances as to the financial stability or viability of any of the hedge
counterparties.
Our management will have broad discretion over the use of the proceeds from our debt issuance and might not apply the proceeds in
ways that increase the value of your investment.
Our management will have broad discretion to use the net proceeds from debt issuance, and you will be relying on the judgment of our
management regarding the application of the proceeds. They might not apply the net proceeds of this offering in ways that increase the value of
your investment. We expect to use the net proceeds from this offering for general corporate purposes, including possible investments in, or
acquisitions of, complementary businesses, joint ventures, services or technologies, working capital and capital expenditures; however, other
than paying the cost of the convertible note hedge (after taking into account the proceeds from the warrant transactions), we have not allocated
these net proceeds for any specific purposes. Our management might not be able to yield a significant return, if any, on any investment of these
net proceeds.
67

Table of Contents
Not applicable.
Not applicable.
Not applicable.
None
Exhibits
The Exhibits listed below are filed as part of this Form 10-Q.
68
ITEM 2.
UNREGISTERED SALES OF EQUITY SECURITIES AND USE OF PROCEEDS
ITEM 3.
DEFAULTS UPON SENIOR SECURITIES
ITEM 4.
REMOVED AND RESERVED
ITEM 5.
OTHER INFORMATION
ITEM 6.
EXHIBITS
Exhibit 3.1(1)
Amended and Restated Certificate of Incorporation of salesforce.com, inc.
Exhibit 3.2(2)
Amended and Restated Bylaws of salesforce.com, inc.
Exhibit 31.1
Certification of Chief Executive Officer pursuant to Exchange Act Rule 13a
-
14(a) and 15(d)
-
14(a), as adopted
pursuant to Section 302 of the Sarbanes
-
Oxley Act of 2002
Exhibit 31.2
Certification of Chief Financial Officer pursuant to Exchange Act Rule 13a
-
14(a) and 15(d)
-
14(a), as adopted
pursuant to Section 302 of the Sarbanes
-
Oxley Act of 2002
Exhibit 32.1
Certification of Chief Executive Officer and Chief Financial Officer pursuant to 18 U.S.C. Section 1350, as
adopted pursuant to Section 906 of the Sarbanes
-
Oxley Act of 2002
Exhibit 101.INS(3)
XBRL Instance Document
Exhibit 101.SCH(3)
XBRL Taxonomy Extension Schema Document
Exhibit 101.CAL(3)
XBRL Taxonomy Extension Calculation Linkbase Document
Exhibit 101.DEF(3)
XBRL Taxonomy Extension Definition Linkbase Document
Exhibit 101.LAB(3)
XBRL Taxonomy Extension Label Linkbase Document
Exhibit 101.PRE(3)
XBRL Taxonomy Extension Presentation Linkbase Document
(1) Incorporated by reference from the Company’s registration statement on Form S-1 (No. 333-111289) Amendment No. 3 as filed with the
Securities and Exchange Commission on April 20, 2004.
(2)
Incorporated by reference from the Company
’
s Form 8
-
K as filed with the Securities and Exchange Commission on April 2, 2009.
(3)
The financial information contained in these XBRL documents is unaudited and these are not the official publicly filed financial statements
of salesforce.com, inc. The purpose of submitting these XBRL documents is to test the related format and technology, and, as a result,
investors should continue to rely on the official filed version of the furnished documents and not rely on this information in making
investment decisions. In accordance with Rule 402 of Regulation S-T, the information in these exhibits shall not be deemed to be “filed”
for purposes of Section 18 of the Exchange Act, or otherwise subject to the liability of that section, and shall not be incorporated by
reference into any registration statement or other document filed under the Securities Act, or the Exchange Act, except as shall be
expressly set forth by specific reference in such filing.

Table of Contents
SIGNATURES
Pursuant to the requirements of the Securities Exchange Act of 1934, the registrant has duly caused this report to be signed on its behalf by
the undersigned thereunto duly authorized.
Dated: November 24, 2010
69
salesforce.com, inc.
/s/ Graham Smith
Graham Smith
Chief Financial Officer
(Principal Financial Officer and Duly Authorized Officer)

Exhibit 31.1
CERTIFICATION
I, Marc Benioff, certify that:
Date: November 24, 2010
1.
I have reviewed this report on Form 10
-
Q of salesforce.com, inc.;
2. Based on my knowledge, this report does not contain any untrue statement of a material fact or omit to state a material fact necessary to
make the statements made, in light of the circumstances under which such statements were made, not misleading with respect to the period
covered by this report;
3.
Based on my knowledge, the financial statements, and other financial information included in this report, fairly present in all material
respects the financial condition, results of operations and cash flows of the registrant as of, and for, the periods presented in this report;
4.
The registrant
’
s other certifying officer and I are responsible for establishing and maintaining disclosure controls and procedures (as
defined in Exchange Act Rules 13a-15(e) and 15d-15(e)) and internal control over financial reporting (as defined in Exchange Act Rules
13a
-
15(f) and 15d
-
15(f)) for the registrant and have:
a)
Designed such disclosure controls and procedures, or caused such disclosure controls and procedures to be designed under our
supervision, to ensure that material information relating to the registrant, including its consolidated subsidiaries, is made known to us
by others within those entities, particularly during the period in which this report is being prepared;
b) Designed such internal control over financial reporting, or caused such internal control over financial reporting to be designed under
our supervision, to provide reasonable assurance regarding the reliability of financial reporting and the preparation of financial
statements for external purposes in accordance with generally accepted accounting principles;
c)
Evaluated the effectiveness of the registrant
’
s disclosure controls and procedures and presented in this report our conclusions about
the effectiveness of the disclosure controls and procedures, as of the end of the period covered by this report based on such
evaluation; and
d) Disclosed in this report any change in the registrant’s internal control over financial reporting that occurred during the registrant’s
most recent fiscal quarter that has materially affected, or is reasonably likely to materially affect, the registrant’
s internal control over
financial reporting; and
5. The registrant’s other certifying officer and I have disclosed, based on our most recent evaluation of internal control over financial
reporting, to the registrant’s auditors and the audit committee of the registrant’s board of directors (or persons performing the equivalent
functions):
a)
All significant deficiencies and material weaknesses in the design or operation of internal control over financial reporting which are
reasonably likely to adversely affect the registrant
’
s ability to record, process, summarize and report financial information; and
b) Any fraud, whether or not material, that involves management or other employees who have a significant role in the registrant’s
internal controls over financial reporting.
/s/ Marc Benioff
Marc Benioff
Chairman of the Board of Directors and Chief
Executive Officer

Exhibit 31.2
CERTIFICATION
I, Graham Smith, certify that:
Date: November 24, 2010
1.
I have reviewed this report on Form 10
-
Q of salesforce.com, inc.;
2. Based on my knowledge, this report does not contain any untrue statement of a material fact or omit to state a material fact necessary to
make the statements made, in light of the circumstances under which such statements were made, not misleading with respect to the period
covered by this report;
3.
Based on my knowledge, the financial statements, and other financial information included in this report, fairly present in all material
respects the financial condition, results of operations and cash flows of the registrant as of, and for, the periods presented in this report;
4.
The registrant
’
s other certifying officer and I are responsible for establishing and maintaining disclosure controls and procedures (as
defined in Exchange Act Rules 13a-15(e) and 15d-15(e)) and internal control over financial reporting (as defined in Exchange Act Rules
13a
-
15(f) and 15d
-
15(f)) for the registrant and have:
a)
Designed such disclosure controls and procedures, or caused such disclosure controls and procedures to be designed under our
supervision, to ensure that material information relating to the registrant, including its consolidated subsidiaries, is made known to us
by others within those entities, particularly during the period in which this report is being prepared;
b) Designed such internal control over financial reporting, or caused such internal control over financial reporting to be designed under
our supervision, to provide reasonable assurance regarding the reliability of financial reporting and the preparation of financial
statements for external purposes in accordance with generally accepted accounting principles;
c)
Evaluated the effectiveness of the registrant
’
s disclosure controls and procedures and presented in this report our conclusions about
the effectiveness of the disclosure controls and procedures, as of the end of the period covered by this report based on such
evaluation; and
d) Disclosed in this report any change in the registrant’s internal control over financial reporting that occurred during the registrant’s
most recent fiscal quarter that has materially affected, or is reasonably likely to materially affect, the registrant’
s internal control over
financial reporting; and
5. The registrant’s other certifying officer and I have disclosed, based on our most recent evaluation of internal control over financial
reporting, to the registrant’s auditors and the audit committee of the registrant’s board of directors (or persons performing the equivalent
functions):
a)
All significant deficiencies and material weaknesses in the design or operation of internal control over financial reporting which are
reasonably likely to adversely affect the registrant
’
s ability to record, process, summarize and report financial information; and
b) Any fraud, whether or not material, that involves management or other employees who have a significant role in the registrant’s
internal controls over financial reporting.
/s/ Graham Smith
Graham Smith
Chief Financial Officer

Exhibit 32.1
CERTIFICATION OF CHIEF EXECUTIVE OFFICER AND CHIEF FINANCIAL OFFICER
PURSUANT TO
18 U.S.C. SECTION 1350,
AS ADOPTED PURSUANT TO
SECTION 906 OF THE SARBANES-OXLEY ACT OF 2002
Based on my knowledge, I, Marc Benioff, certify, pursuant to 18 U.S.C. Section 1350, as adopted pursuant to Section 906 of the Sarbanes-
Oxley
Act of 2002, that the Quarterly Report of salesforce.com, inc. on Form 10-Q for the period ended October 31, 2010 fully complies with the
requirements of Section 13(a) or 15(d) of the Securities Exchange Act of 1934 and that information contained in such Form 10-
Q fairly presents,
in all material respects, the financial condition and results of operations of salesforce.com, inc.
Based on my knowledge, I, Graham Smith, certify, pursuant to 18 U.S.C. Section 1350, as adopted pursuant to Section 906 of the Sarbanes-
Oxley Act of 2002, that the Quarterly Report of salesforce.com, inc. on Form 10-Q for the period ended October 31, 2010 fully complies with
the requirements of Section 13(a) or 15(d) of the Securities Exchange Act of 1934 and that information contained in such Form 10-Q fairly
presents, in all material respects, the financial condition and results of operations of salesforce.com, inc.
/s/ Marc Benioff
Marc Benioff
Chairman of the Board of Directors and Chief
Executive Officer
/s/ Graham Smith
Graham Smith
Chief Financial Officer
